Gain insights from Cloud Services using the latest version of Splunk Enterprise Security 4.7

Our customers use Splunk Enterprise Security (ES) as an analytics-driven SIEM to quickly detect threats, respond to attacks, ransomware, to accelerate responses across their cloud and on-premises deployments.
The latest version of Splunk ES, version 4.7 introduces key enhancement to improve investigation efficiency and provides insight from common SaaS apps:
- Expands visibility and insight you can gain from common SaaS apps such as Salesforce.com, Office365, AWS, Box, Okta and more.
- Improves Investigation Efficiency and Incident Response.
- Enhances collaboration and user experience with persona centric navigation and workflow improvements.
Meeting the needs of Cloud adoption, Threat Intelligence and persona-based use cases
Customers continue to adopt SaaS apps and the trend of workloads and data moving to the Cloud continues to grow. Office 365 is the most popular SaaS app, with Salesforce, Box, AWS rounding out top 4 list {Source: Businesses at Work, 2017 Okta}
Gartner has indicated that by 2018, 60% of enterprises that implement cloud visibility and control tools will experience one-third fewer security failures. {Source: Is the Cloud Secure? Gartner Research 2017}
The continued adoption of Cloud/SaaS services expands the threat vectors and Enterprises now need to monitor user activity, application access from not only Cloud/SaaS services but from on-premises services as well to determine the full scope of potential threats and attacks.
However, the visibility provided by SaaS tool vendors is limited, tends to be expensive and presents a siloed view.
From a Security operations perspective, a key metric is time to investigate and respond, which has been aided by the continued adoption of Threat Intelligence. In a recent survey by SANS, 69% of the respondents said that Threat Intel helps with prevention and detection, while 71% said that it helps Response as well. {Source: The SANS 2017 CTI Survey}
Gain Insight from Enterprise SaaS Apps
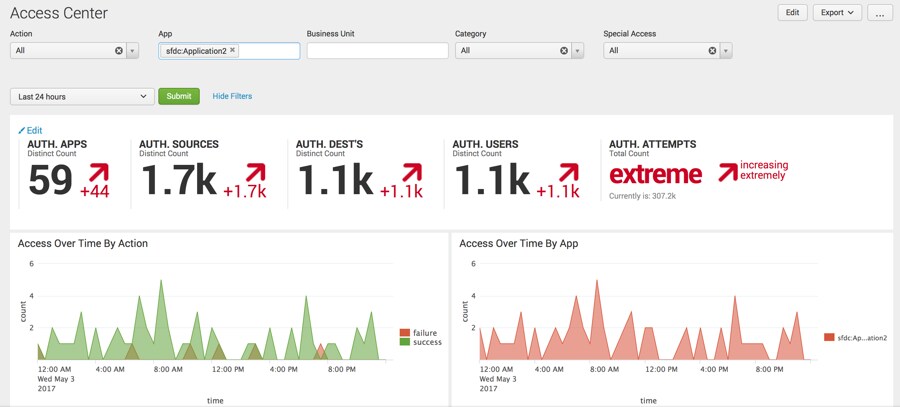 With Splunk ES 4.7, you can gain visibility, by directly using data from SaaS apps. You can use SaaS specific data for correlation or display within existing Splunk ES dashboards, such as Access Center.
With Splunk ES 4.7, you can gain visibility, by directly using data from SaaS apps. You can use SaaS specific data for correlation or display within existing Splunk ES dashboards, such as Access Center.
As is common with Splunk, you can always create use case centric dashboards -- panels to suit your needs and workflow. As part of this release, Splunk Enterprise Security(ES) was validated with common SaaS apps, which map to the Splunk Common Information Model. This is a huge benefit to existing customers as well. i.e., if you are an existing ES customer (say ES 4.5), you can immediately gain insight from these popular SaaS Apps!
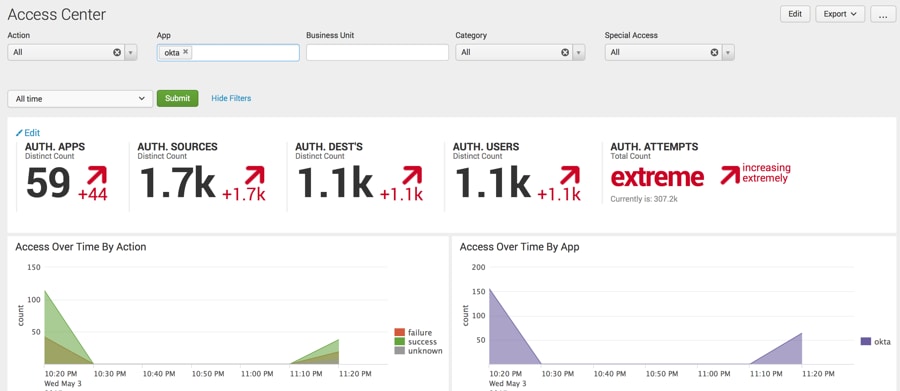 Within Splunk ES you can get context from popular Enterprise SaaS apps, correlate across SaaS and on-premise sources to improve investigation response. You can now monitor, discover, determine and report on the scope of user activity, network activity, endpoint activity, access activity and abnormal activity from popular SaaS apps within your environment.
Within Splunk ES you can get context from popular Enterprise SaaS apps, correlate across SaaS and on-premise sources to improve investigation response. You can now monitor, discover, determine and report on the scope of user activity, network activity, endpoint activity, access activity and abnormal activity from popular SaaS apps within your environment.
Improves Investigation Efficiency and Incident Response
Determine full scope of activity by using Asset and Identity Associations
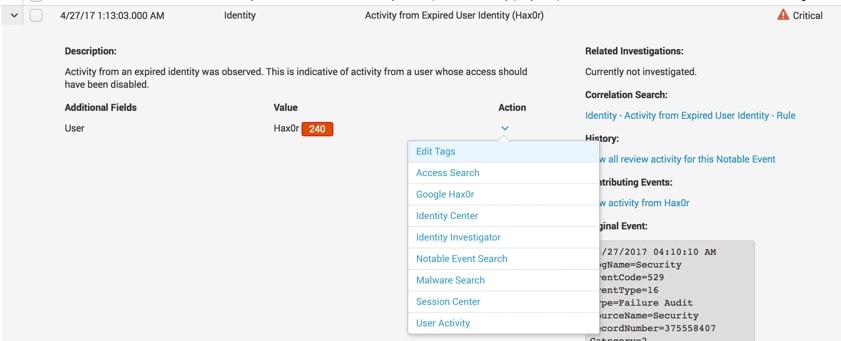 Now, you can determine the activities of potential threat actors within the SIEM investigation workflow by using User behavior Analytics (UBA) determined asset and identity associations.
Now, you can determine the activities of potential threat actors within the SIEM investigation workflow by using User behavior Analytics (UBA) determined asset and identity associations.
An analyst/investigator investigating an Incident can now determine all activity associated with a user/entity and the device within the notable event and take next steps.
From within Incident Review, the investigator can initiate a Workflow action which will lead to the Session Center or the user can directly navigate to the Session Center Dashboard.
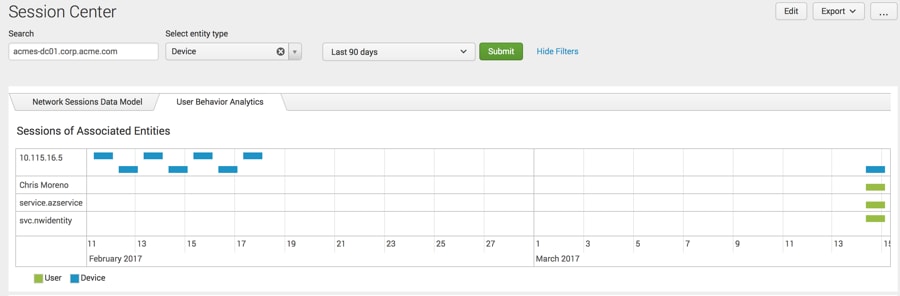 This capability requires integration with Splunk UBA. While investigating an Incident within ES, the Investigator can view the activities from the associated IP Address, Mac, hostname and identify the time range of all associated activity. Now, you can identify user accounts and devices associated with devices during specific sessions, and devices associated with users during specific sessions.
This capability requires integration with Splunk UBA. While investigating an Incident within ES, the Investigator can view the activities from the associated IP Address, Mac, hostname and identify the time range of all associated activity. Now, you can identify user accounts and devices associated with devices during specific sessions, and devices associated with users during specific sessions.
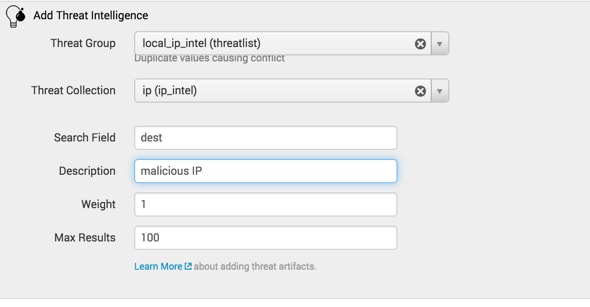
 Easier to retrieve and take actions using Threat Intelligence
Easier to retrieve and take actions using Threat Intelligence
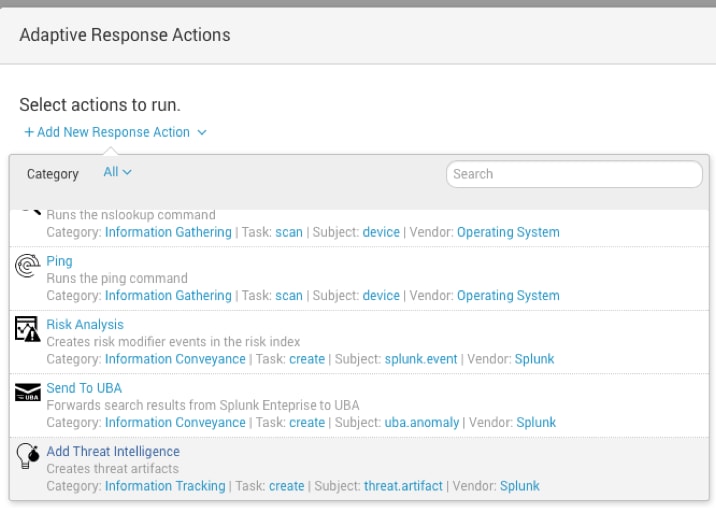
This version adds support for Automated Indicator Sharing(AIS), which is the US Department of Homeland Security’s initiative to enable the exchange of threat indicators between the Government and private sector.
AIS complements and leverages the Structured Threat Information Expression (STIX) and Trusted Automated Exchange of Indicator Information (TAXII) specifications which are supported by the Threat Intelligence framework within Splunk Enterprise Security.
Splunk ES now allows manual or automated additions of indicators to Threat Lists. From within Incident Review you can add threat intelligence as an ad-hoc adaptive response action to determine the full extent of an incident under investigation.
Enhance collaboration and user experience with persona-centric navigation and workflow improvements.
Gain persona based and use case specific views by customizing navigation with enhanced UI components.
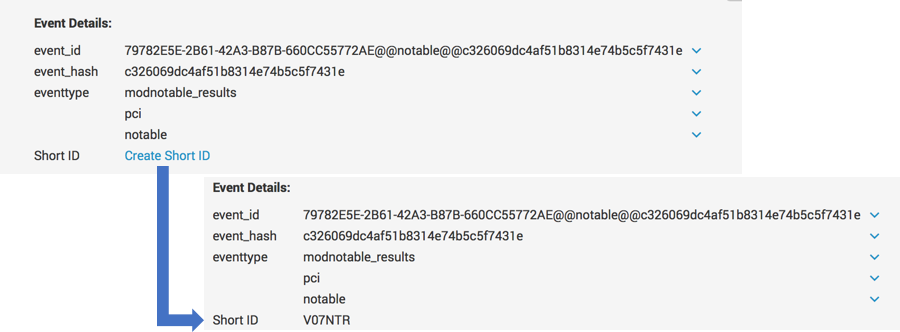
Analysts and Investigators can better collaborate during incident investigation by using short identifiers. Short identifiers are 7 digit characters.
You can generate a short ID for notable events in Incident Review, allowing you to communicate with people on your team about a specific event more easily. In addition to ease of collaboration, it is easy to use and investigate.
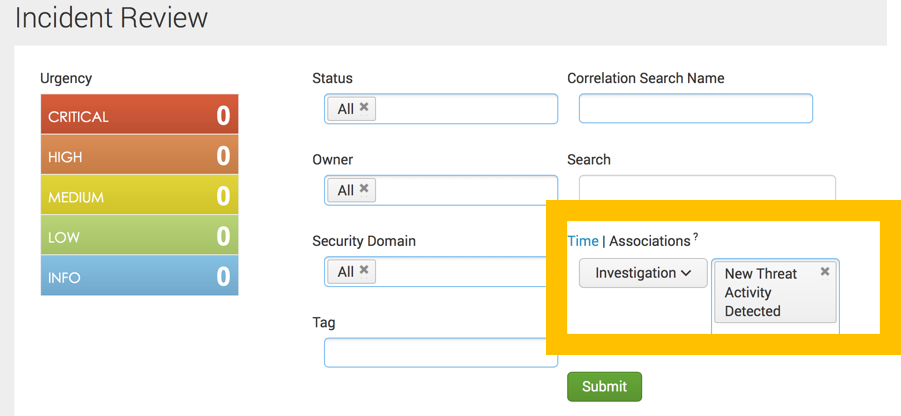
You can now simplify investigations by determining notable event and investigation associations from within the Incident Review view. From within the Incident Review dashboard, a user can easily determine which notable events are associated with investigations by filtering on Incident Review by specific investigations or Short Id.
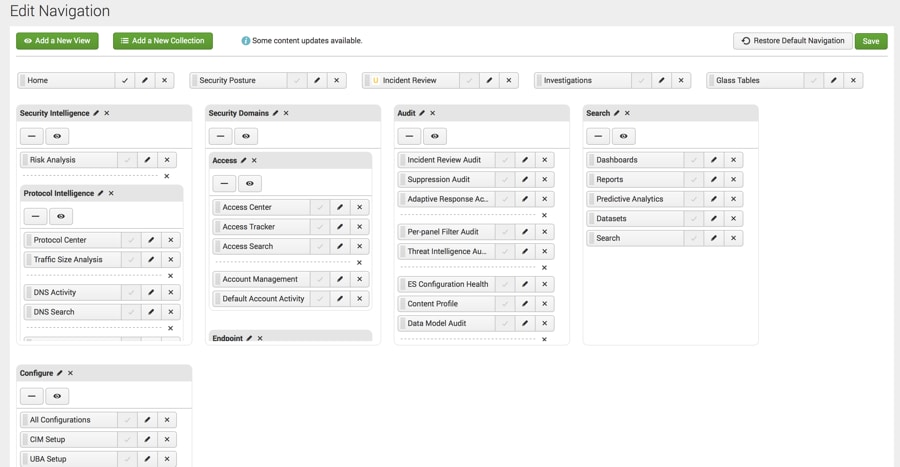
 It is now easy for admins to implement use case and persona specific views and improve efficiency using customizable navigation.
It is now easy for admins to implement use case and persona specific views and improve efficiency using customizable navigation.
The navigation editor lets you to customize Splunk Enterprise Security layout, dashoards to solve the use cases that are relevant to you. Additionally, it highlights the new views and collections and updated, or deprecated views. Now you can easily restore the default menu configuration, and customizations that were previously made to the navigation.
If you are an existing Splunk Enterprise Security customer, you can download the latest version here.
If you are not familiar with Splunk Enterprise Security, use the free 7 day Cloud sandbox.
Contact us to find out how customers are already reducing investigation and remediation times by automating decisions or by using human-assisted decisions.
Join us next week at Infosecurity Europe in London and at the Gartner Security and Risk Management Summit during June 12-15 in National Harbor, MD for more details.
Thanks,
Girish
----------------------------------------------------
Thanks!
gbhat
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.