Securing a New Way of Working: You Gotta Love the CVEs
Right, so now the vast majority of your workforce works remotely. Clearly managing all these inbound VPN connections is on top of mind, but what about other vulnerabilities you should be monitoring for?
In addition to the ever increasing number of inbound VPN connections, organizations can expect an increase in the use of SaaS-based collaborative software such as Slack, Dropbox, G Suite, and Trello. In addition to implementing strict policies on applications that can be installed on enterprise laptops, one should also continuously monitor for related vulnerabilities. We’re seeing attackers with the ability to write exploit code within a day of the vulnerability release.
Some things to look for include:
Dusting off VPN concentrators to bolster your remote workforce capability? Are you sure they are patched? Make sure you are Monitoring for VPN-related vulnerabilities on VPN (the most recent ones being CVE-2020-5180 and CVE-2020-6760 )
Monitoring for vulnerabilities related to software that employees will use significantly more such as Google Docs (CVE-2019-7250), Zoom, or Slack
NIST National Vulnerability Database — VPN
 Vulnerability scans from vendors like Nessus and Qualys will be important to understand the attack surface of the network. Scans must also be run with the most recent vulnerability checks. Once the scans with the correct checks run, you can see the scan results and look at VPN vulnerabilities. SSE has a great search example that allows for CVE searching. If you look for all settings on and vulnerabilities, you’ll find an example named Ransomware Vulnerabilities.
Vulnerability scans from vendors like Nessus and Qualys will be important to understand the attack surface of the network. Scans must also be run with the most recent vulnerability checks. Once the scans with the correct checks run, you can see the scan results and look at VPN vulnerabilities. SSE has a great search example that allows for CVE searching. If you look for all settings on and vulnerabilities, you’ll find an example named Ransomware Vulnerabilities.
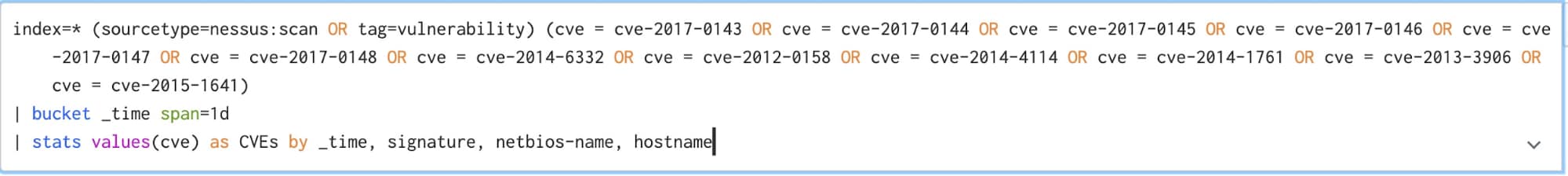
In the upper right-hand corner, you can switch the SPL mode to Live data and you’ll see the SPL change to what you see below.
From here you can plug in the CVE you’re looking for as new vulnerabilities are released and scanned.
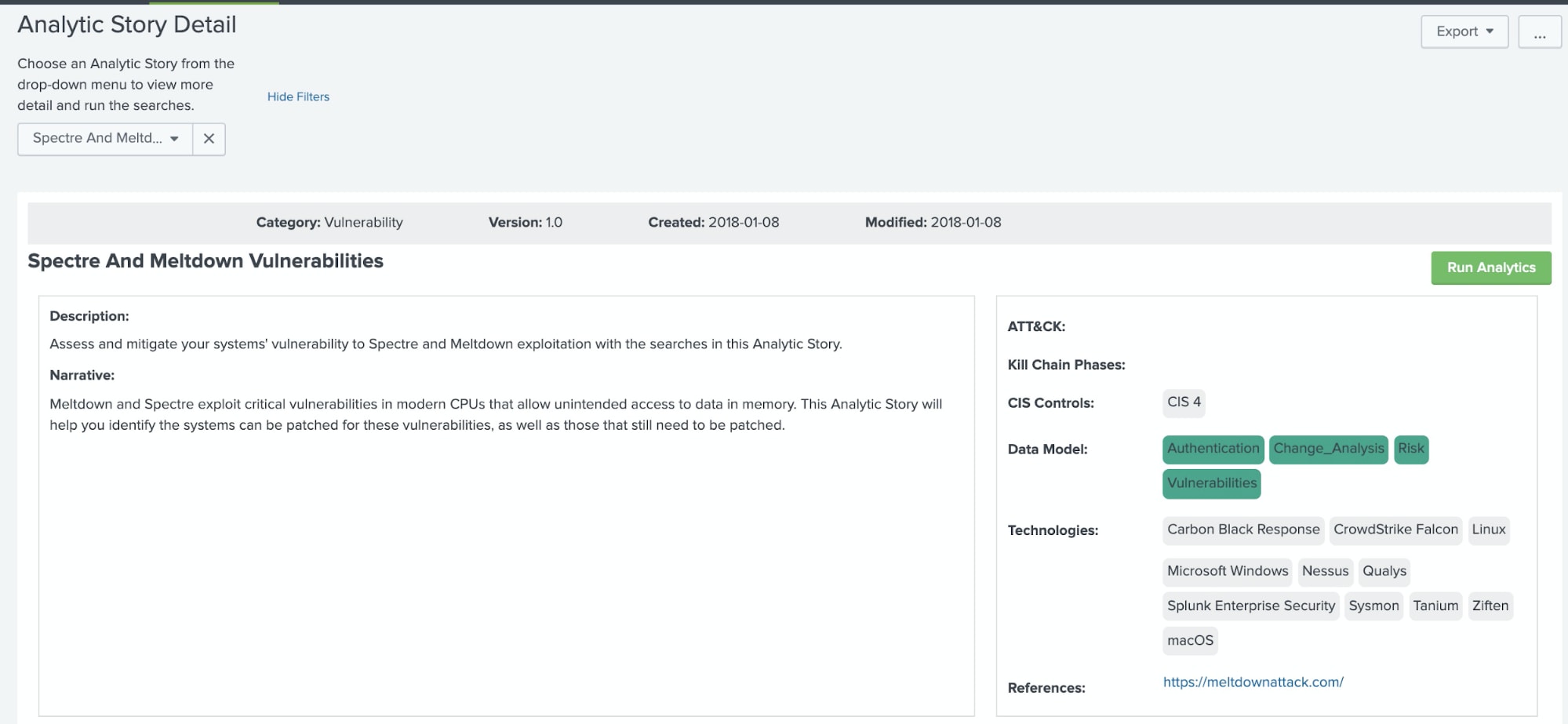
Furthermore, if you are using Enterprise Security today, then you’re probably already aware that there are 63 Analytic Stories published by Splunk’s Security Research Team in the Enterprise Security Use Case Library.
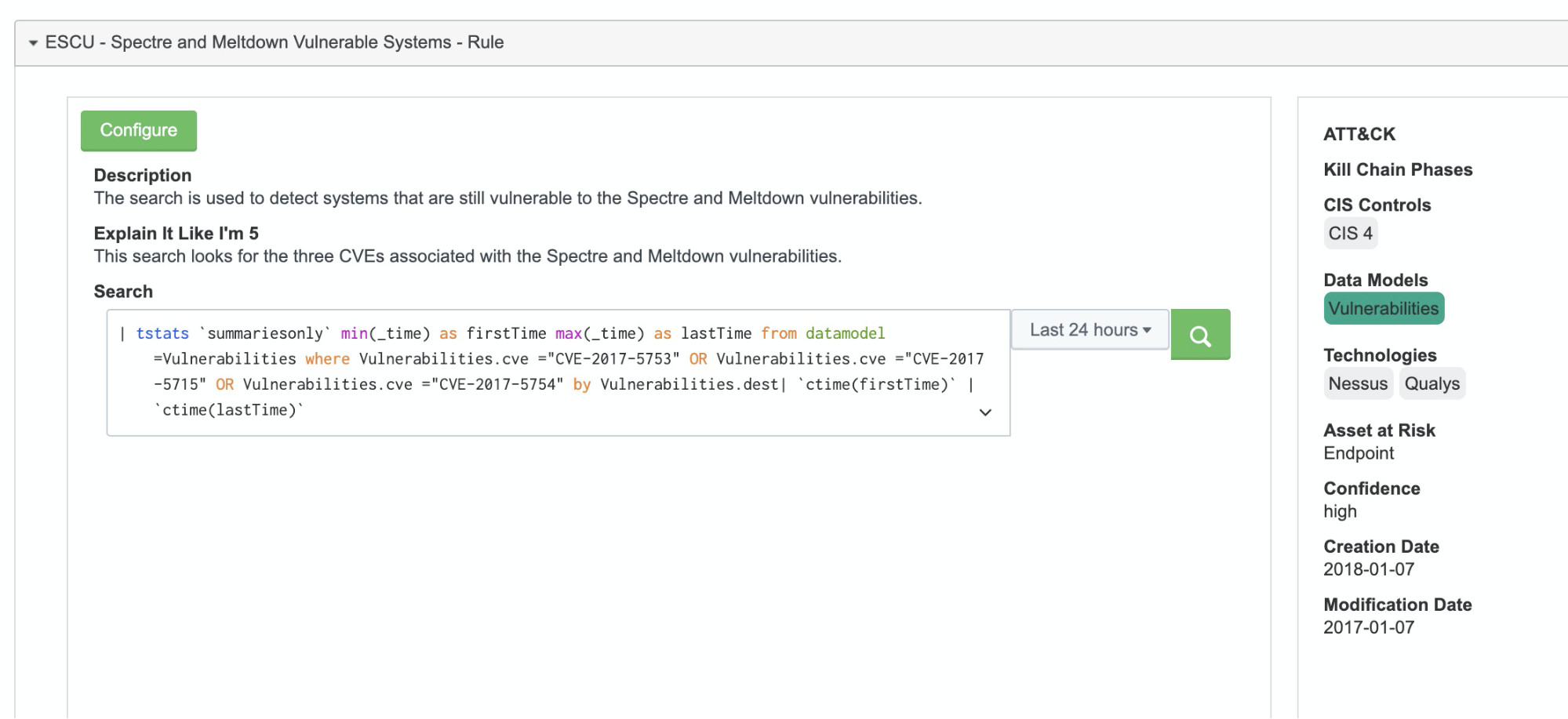
Take a minute to review the Analytic Story on Spectre and Meltdown Vulnerabilities.
Analytic Story: Spectre and Meltdown Vulnerabilities
We won’t be necessarily focusing the Spectre and Meltdown vulnerability CVEs which are in the SPL example. This SPL example uses tstats and is easy enough to look for the latest vulnerabilities on nvd.nist.gov and modify the SPL for the vulns that interest you the most based on your data sources. Because we’re using tstats the data will have to be CIM (Common Information Model) compliant with the correct TA (Technology add-ons) and data populating the data models.
- https://docs.splunk.com/Documentation/Splunk/latest/SearchReference/Tstats
- https://docs.splunk.com/Documentation/CIM/latest/User/Overview
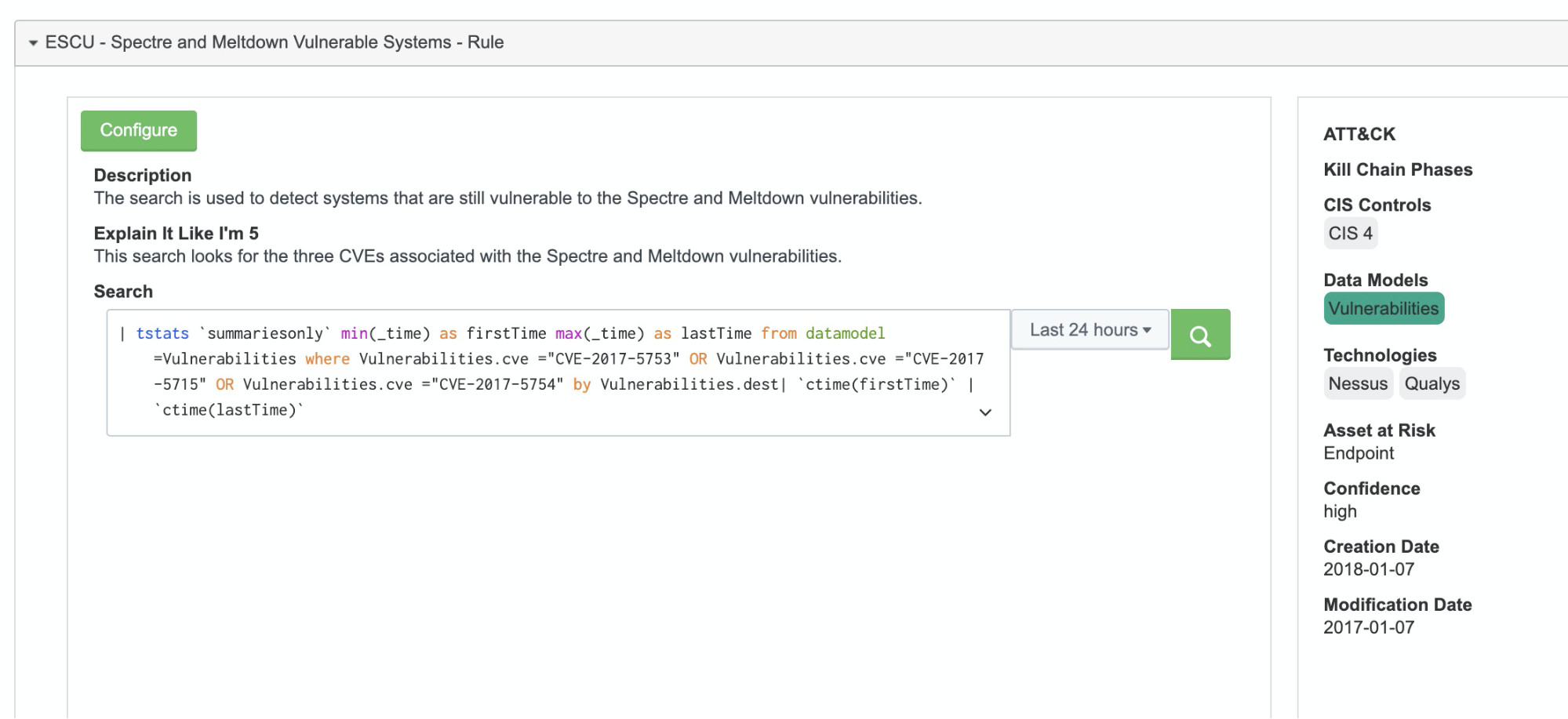
Example searches include Spectre and Meltdown Vulnerable Systems and Systems ready for Specter-Meltdown Windows Patch. The required data sources here are EDR tools and vulnerability scanning technologies such as Qualys and Nessus.
Check here for more practical guides on how to secure your organization in the new work-from-home era.
Thanks to the contributors of this blog post, Bryan Sadowski, Lily Lee, Rene Aguero, James Brodsky, Chris Simmons.
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




