Securing a New Way of Working: Monitoring Those Endpoints
With more and more endpoints accessing your network remotely, you should expect rapid increases in VPN connections and usage, as well as exponential usage of cloud-based services. There are numerous Splunk apps that can help you increase the monitoring of remote endpoints but let’s showcase Splunk Security Essentials (SSE). SSE is a free app that aims at making security simpler and allows you to validate data sources, capabilities, test and implement detections mapped to cybersecurity frameworks like MITRE ATT&CK and many more. You can download the app in Splunkbase.
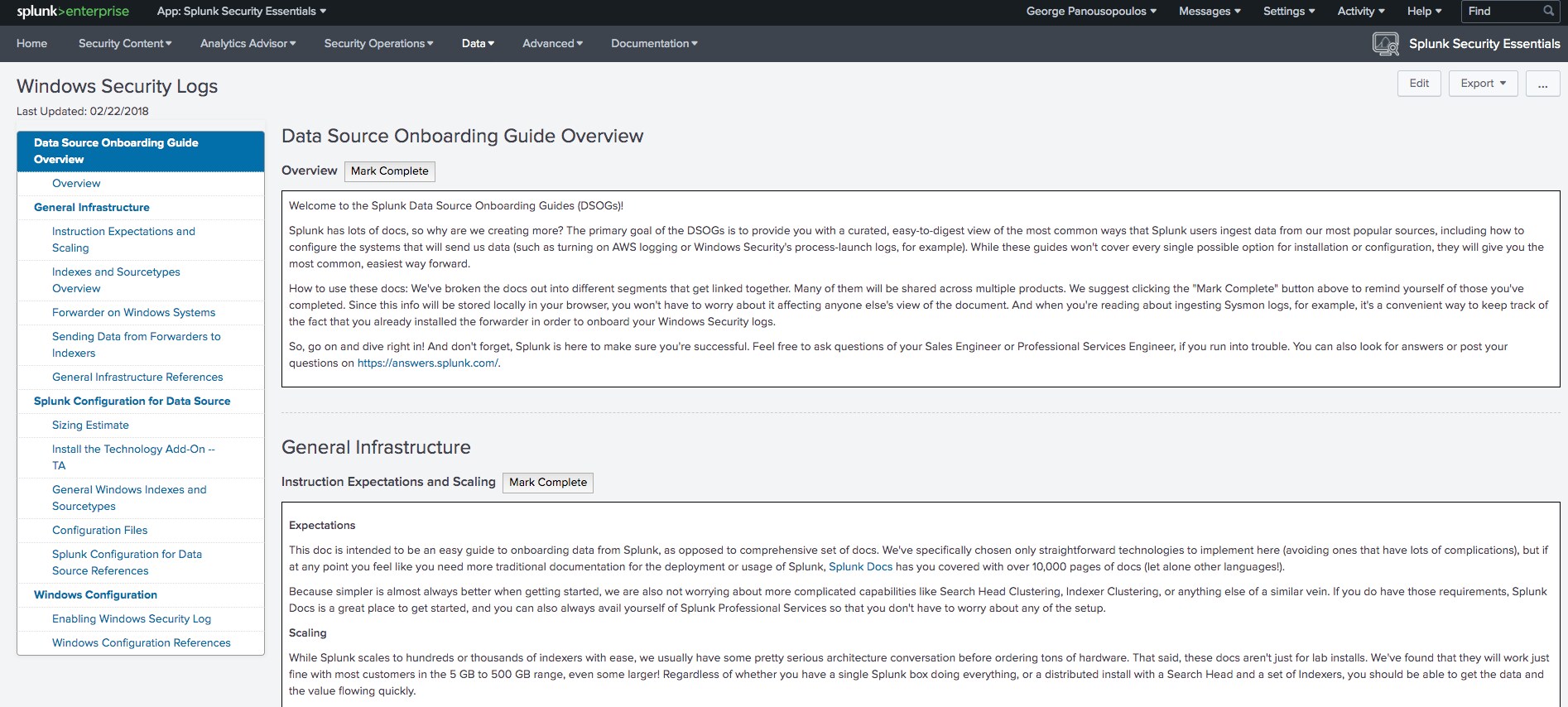
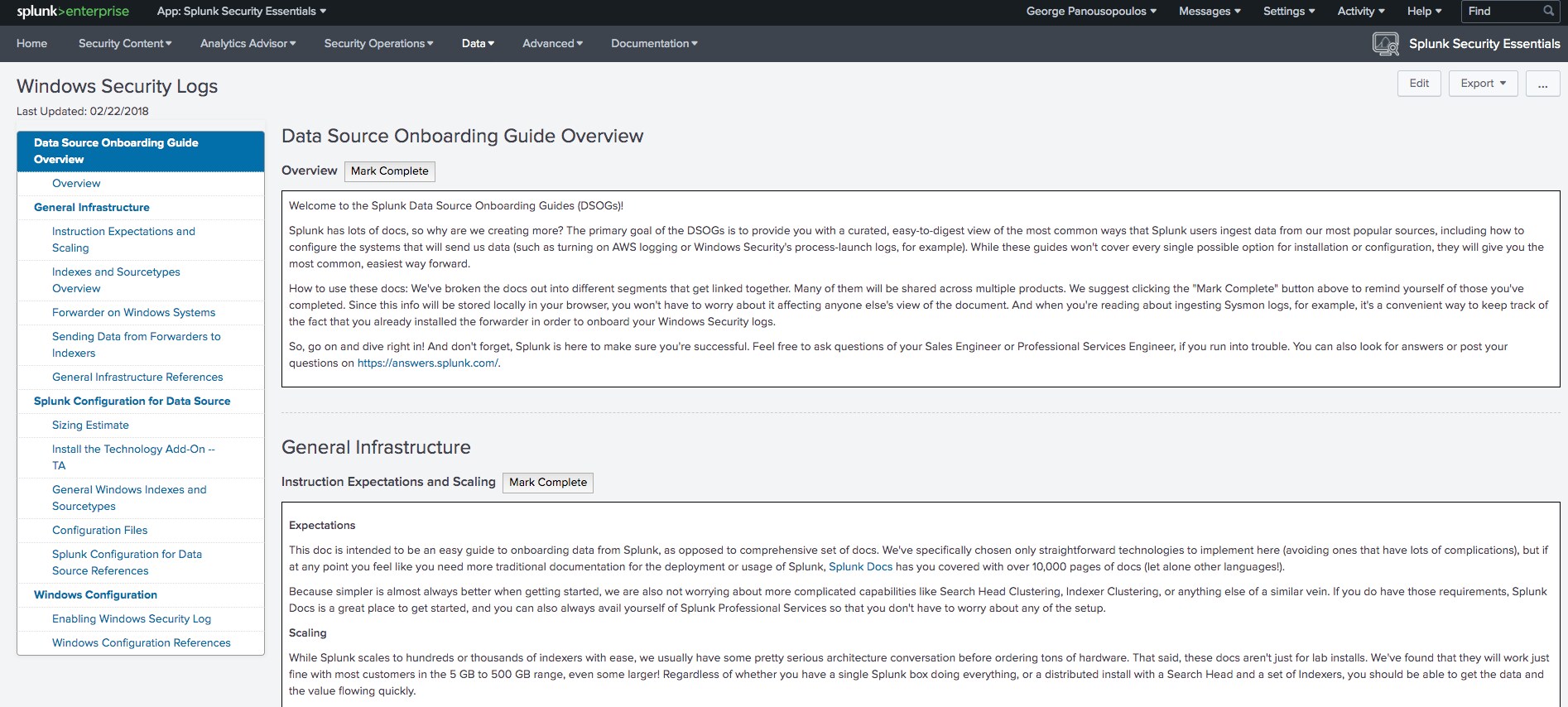
It’s highly likely that you are already monitoring Windows hosts but if you want to on-board Windows Security Logs — using the free Splunk Universal Forwarder, for example — you can check the on-boarding guide provided by SSE:
If you want to monitor Linux servers, here is a good starting point for getting these logs into Splunk. And don’t forget you can work some magic with OSQuery too.
All Data Source Onboarding Guides in SSE ship with instructions and guidance articles to help you onboard and implement the relevant detections. In addition to Windows Security Logs, you might be interested in monitoring Endpoint Detection and Response (EDR) data. In this case, you can use the available onboarding guides which are quite extensive, such as Windows Process Launch Logs or Microsoft Sysmon; following this great guide, "Peeping Through Windows (Logs)," will also help. Another great resource to get you started with logging for incident response purposes is this collection of cheat sheets. The EDR and Windows Security Logs data-sources combined can be used for 140+ detection including Account Compromise with Suspicious Internal Activity and Suspicious Data Movement, all documented in the app.
Account compromise, in particular, becomes more relevant as the risk for the exposure of your employees’ endpoints increases due to factors outside your control—i.e. users might be connecting via a public wi-fi hotspot or have no security applied on their home router making them more vulnerable to attacks.
Having looked into tips for onboarding data and monitoring your endpoints, it’s probably a good time to look at the additional guides our security experts have released on securing your organization in a new working-from-home era.
Thanks to the contributors of this blog post, Bryan Sadowski, Lily Lee, Rene Aguero, James Brodsky, Chris Simmons.
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




