I Do Not Like Your Ransom Scam. I Do Not Like It, SamSam I Am.
Happy New Year 2019! The Splunk Security Research Team collectively gained about 15 pounds over our winter break (all muscle, of COURSE). That said, despite all of the revelry and carbs, we never stopped thinking about how to better protect you from the evils lurking out there in cyberspace.
While we were busy overeating, the US Department of Justice (DOJ) was busy charging Faramarz Shahi Savandi, 34, and Mohammad Mehdi Shah Mansouri, 27, both of Iran, in a 34-month-long international computer hacking and extortion scheme involving the deployment of the SamSam ransomware, which was first identified in 2015. According to the DOJ, the malicious software has affected thousands of victims (as many as one per day day) so far and has raised almost $6M in ransom. The total losses caused by the ransomware have risen to about $30M, according to DOJ.
Although categorized under the heading of ransomware, SamSam has some important differences from the more elementary types of malware in this category. For example, conventional ransomware is a numbers game. Perpetrators use a "spray-and-pray" approach, charging a small ransom (typically under $1,000). The goal is to find a large number of victims willing to pay these mini-ransoms, adding up to a lucrative payday. They use relatively simple methods for infecting systems, such as email-based phishing campaigns and drive-by downloads.
In contrast, SamSam attacks have become progressively more targeted and skillful. First, the SamSam actors break into a victim’s network using tools like NLBrute or JexBoss, surveil it, and then move laterally to find and delete any existing data backups. At that point, they execute the malware. The attacks are tailored to cause maximum damage and the threat actors usually demand amounts in the tens of thousands of dollars. What's more, unlike with typical ransomware (Wannacry, for example), SamSam does not employ crypto worms. Instead, it requires the attacker to have enough skill to gain access to the individual environment. Next, the actors escalate their privileges to admin level. They scan the networks for worthy targets, using conventional tools, such as PsExec or PaExec, quickly encrypting files.
An Analytic Story recently released in Splunk's Enterprise Security Content Updates (ESCU) app includes searches designed to help detect infection vectors and behavioral signs of this dangerous ransomware, such as writes to system32, writes with common ransomware extensions, batch files under system32, and remote desktop protocol (RDP) brute-force attacks. To leverage this story, as well as the more expanded story entitled "Ransomware," download and install the latest version of ESCU from Splunkbase.
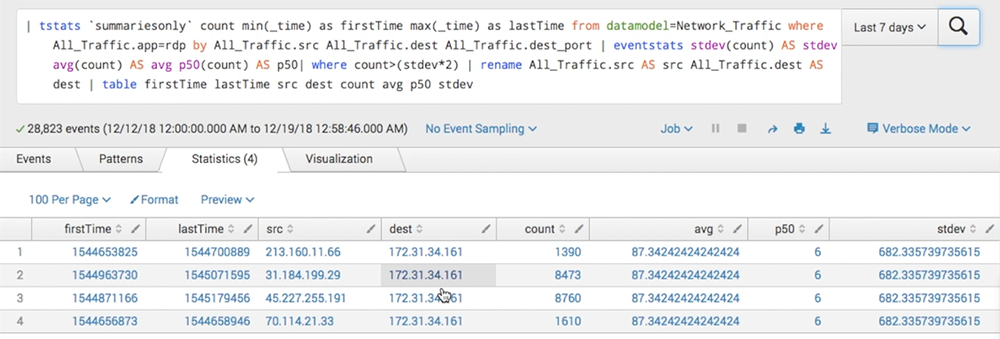 Above is an example of results from the "Remote Desktop Network Bruteforce" search included in the SamSam Ransomware Analytic Story. This search looks for RDP application network traffic and filters any source/destination pair generating more than twice the standard deviation of the average traffic.
Above is an example of results from the "Remote Desktop Network Bruteforce" search included in the SamSam Ransomware Analytic Story. This search looks for RDP application network traffic and filters any source/destination pair generating more than twice the standard deviation of the average traffic.
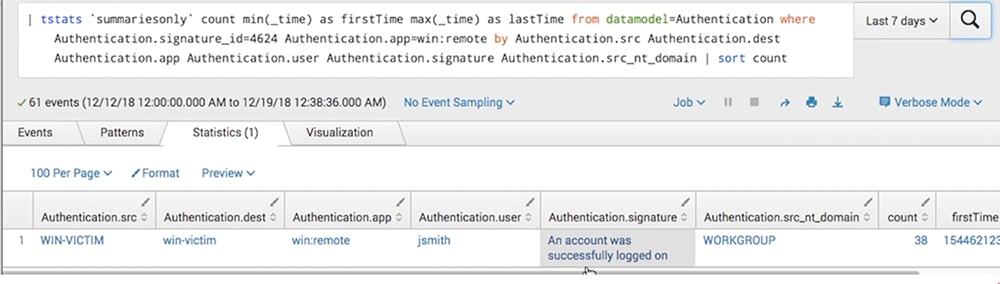 After identifying suspicious RDP activity, use the provided investigative search to probe more deeply, as in the screenshot above.
After identifying suspicious RDP activity, use the provided investigative search to probe more deeply, as in the screenshot above.
Also in the latest release are improvements to the Apache Struts Vulnerability story, which helps you detect and investigate activities (such as unusually long content-type length, suspicious java classes and web servers executing suspicious processes) consistent with attempts to exploit Apache Struts vulnerabilities. One of the new searches looks for invocation of suspicious Java classes that are commonly employed in remote code-execution vulnerabilities (RCEs). Another search helps you investigate the user-agent and destination URLs for web POST requests that have been assigned a source IP. This search will help you easily characterize suspicious traffic.
The Splunk Security Research Team sleeps better at night when we know you are protected against threats. So download ESCU version 1.0.32 from Splunkbase today!
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.