Cities Held Hostage: Fighting Ransomware with Analytics

A series of ransomware attacks on U.S. city government offices recently made news after 20 municipalities were targeted. In a report, the FBI Cyber Division described the targets of these payloads as "varied and indiscriminate," acknowledging that small municipalities were amongst the sectors most frequently hit by this spate of ransomware attacks. Against the agency's guidance, some cities paid ransom to obtain keys to decrypt data in these attacks.
Although the New York Times reported that stolen and subsequently leaked NSA exploitation code was part of the attack chain that affected these cities, this fact has been refuted, at least in one case. In some instances, these payloads have been listed as common ransomware. The series of ransomware attacks highlights the importance for organizations, no matter their size or budget, to be prepared.
The Splunk Security Research Team has been continuously producing defense measures against ransomware. In this blog post, we'll take a quick look at the recent campaigns against municipalities and explore the use of Splunk detection/investigation searches enhanced with ReversingLabs TitaniumCloud.
Why is ransomware so successful?
The ransomware attacks above were considered "successes," since the ransoms were paid. And it is no mystery why the cities buckled under the pressure: the effects of these types of attacks can be immediate, bringing down online services/payment transactions, related physical services, real estate transactions, and more.
The bottom line is that ransomware is effective because the cost of decrypting the data (both in time and in computation cost) is often higher than the ransom itself. In some cases, they are crimes of opportunity, enabled by sloppy IT departments who fail to perform basic updates and backup practices. In others, it's poorly trained end users who bypass security controls and execute malicious payloads or visit malicious sites, exposing themselves to exploitation.
The main driver of these attacks is financial and is driven by the use of cryptocurrency. Cryptocurrency provides an acceptable level of anonymity for criminals, who can request and accept digital currency transactions without oversight or regulation anywhere in the world. According to a report by RecordedFuture, the percentage of victims paying ransomware has increased by 17.1% for government entities and up to 45% in other segments, demonstrating just how big the problem has become.
The actors
 |
| *Image from Armor blog |
Not all of the facts in these cases have been released, so it is difficult to come to a confident conclusion about the specific actors or their motivations. One theory is that organized crime was the source of these attacks, based on the high number of municipalities (such as the three in Florida, referenced above) that were targeted. Coordinated or not, there is definitely a pattern that indicates that attackers used the same or a similar tool. Another possibility is that the cities use a common application--one with vulnerabilities that were leveraged by the attackers.
In many cases, the use of ransomware is the final step in the attack chain. Malicious actors achieve persistence, move laterally, identify information assets, and exfiltrate valuable data that can be bartered in dark markets. It has been reported that some of these payloads do not possess the ability to spread themselves and likely were spreading by post-exploitation tools. Finally, they can drop ransomware and wait to cash their ransom money.
The payloads
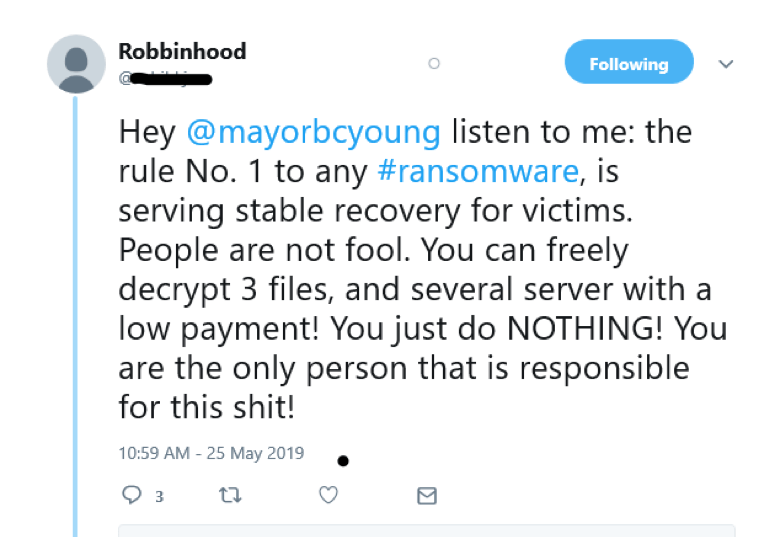
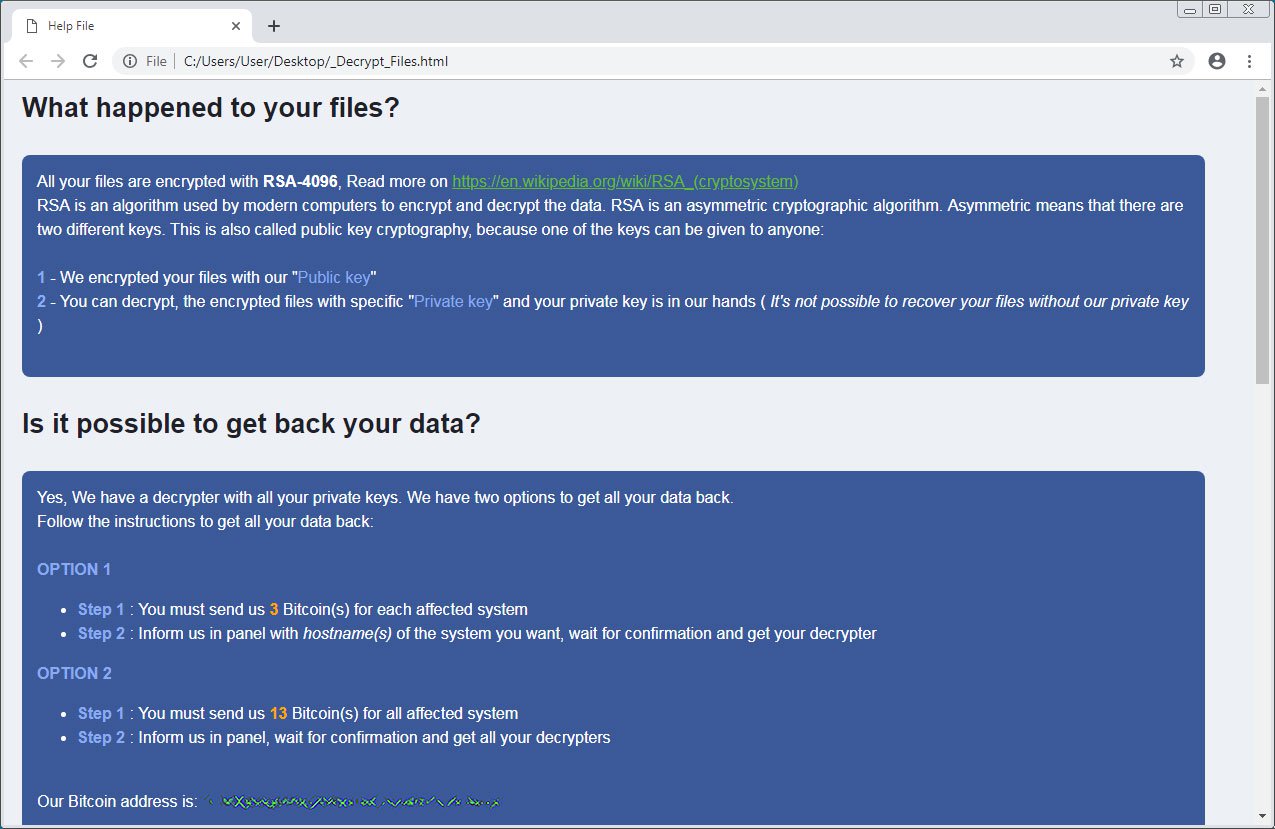 |
| *Ryuk/Robbinhood ransomware notes * Crowdstrike *Bleeping Computer |
There are two known ransomware payloads used in these attacks on municipalities—Robbinhood and Ryuk. There are commonalities between these two payloads. Both of them:
- Terminate processes/thread
- Reference kernel32dll (Windows NT Base API Client DLL)
- Contain references to mscoree.dll (.NET runtime execution engine)
- Detect OS version, enumerate disk drives, path, directories, and files
- Create/access network shares
- Disable volume shadow copy services (prevent backup)
- Enumerate system information/variables
Ryuk uses RSA-2048/AES-256 to encrypt files and append a .ryk extension, whereas RobbinHood uses AES/RSA-4096 to encrypt files and append its .enc_robbinhood extension.
Not surprisingly, some of these ransomware payloads have been observed in conjunction with other types of crimeware. It is not uncommon for different actors to adapt and deploy payloads based on the perception of various campaigns' success. Based on this successful string of ransomware attacks on municipalities, it is likely that malicious actors will continue adapting and pairing different malicious code with Ryuk and Robbinhood ransomware.
Tactical SIEM
It is possible to address these ransomware threats with Splunk. The following example is an investigation of a suspicious hash, using a hash associated with the RobbinHood ransomware.
In this case, we created a workflow action using an MD5 hash. This hash can be indexed or obtained with any applicable endpoint product that can produce MD5 hashes for files.
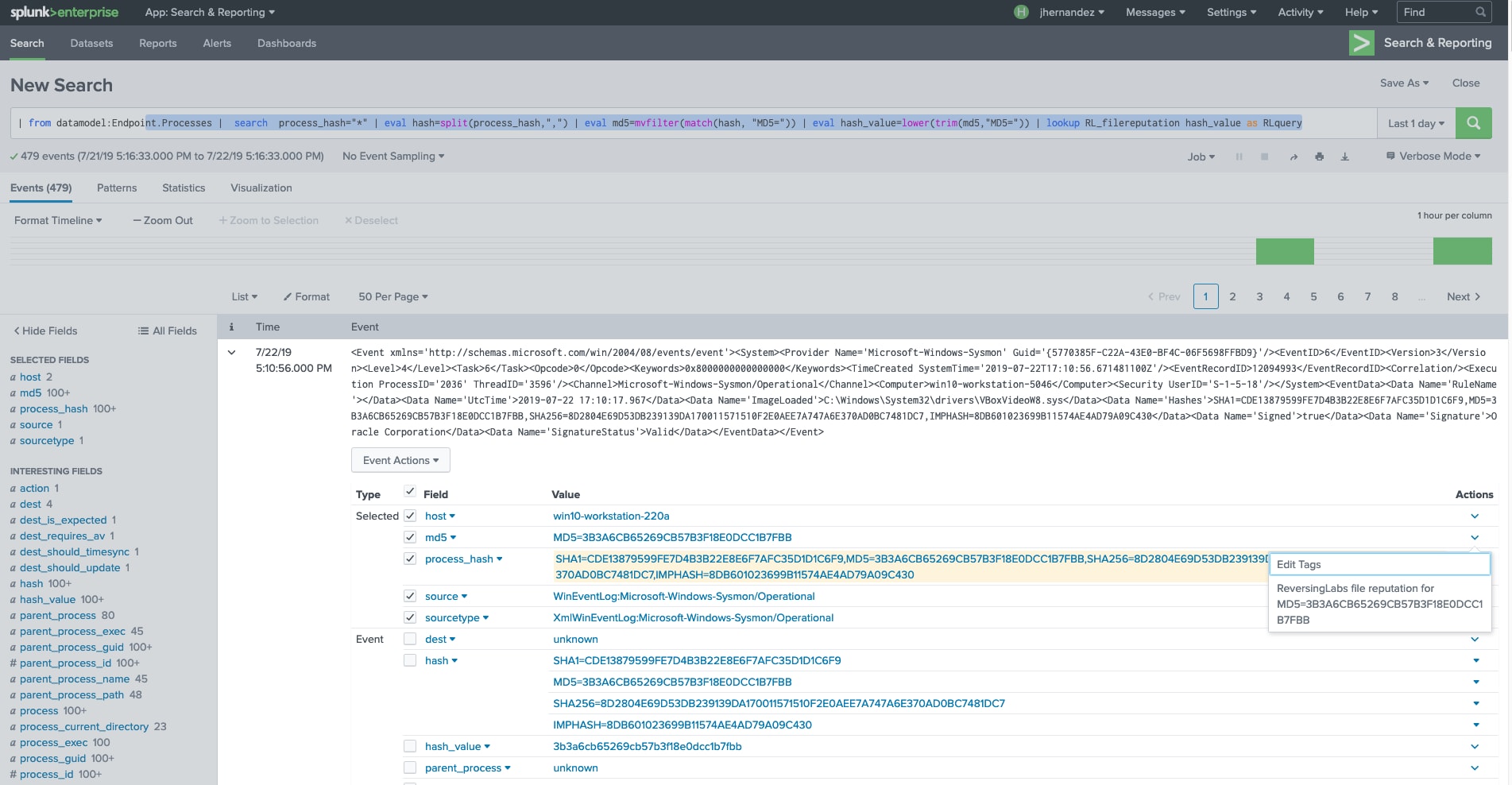 |
| Workflow Action display when clicking on a field with an MD5 hash in this case. |
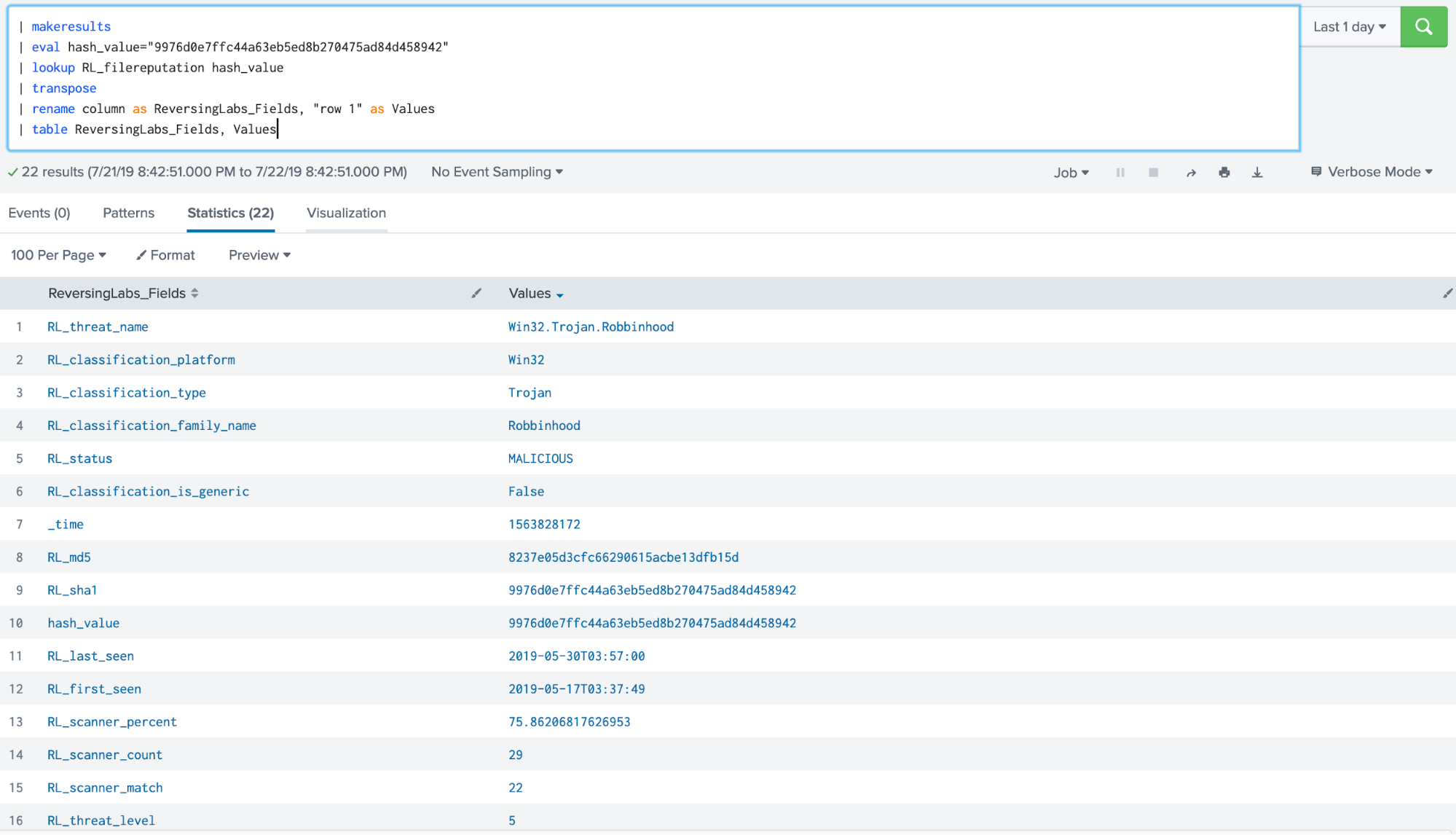
Once we have identified the targeted hash, we can use the lookup function from the ReversingLabs External Lookup for Splunk app.
ReversingLabs MD5 hash search
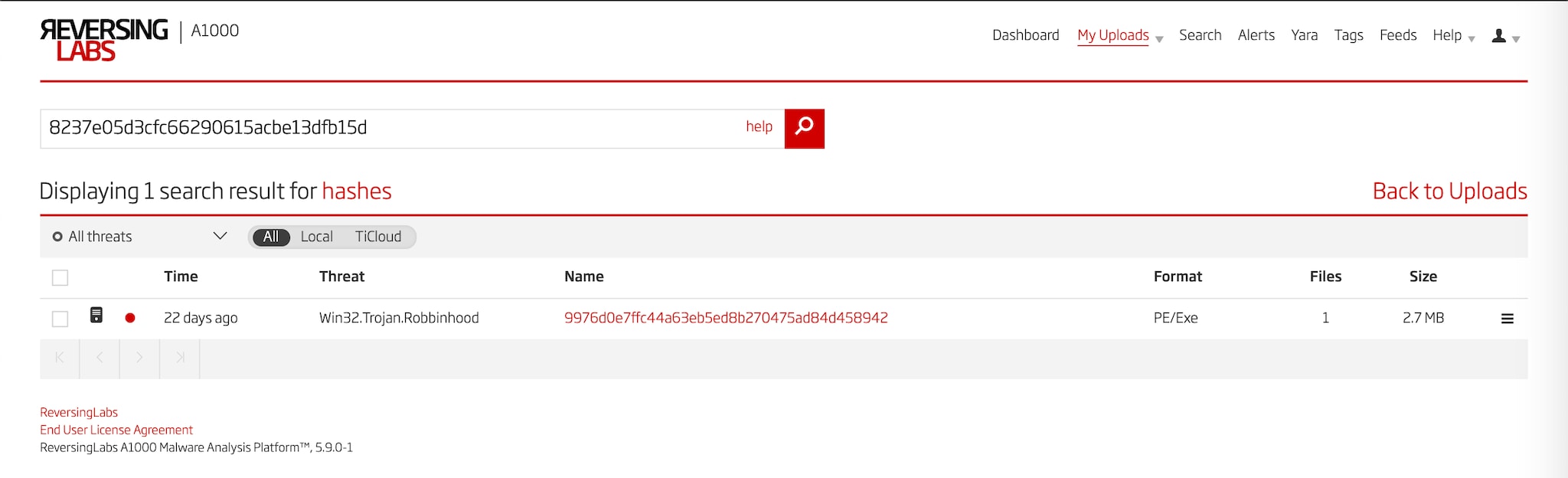
We can also use the function directly via Splunk search, as seen below.
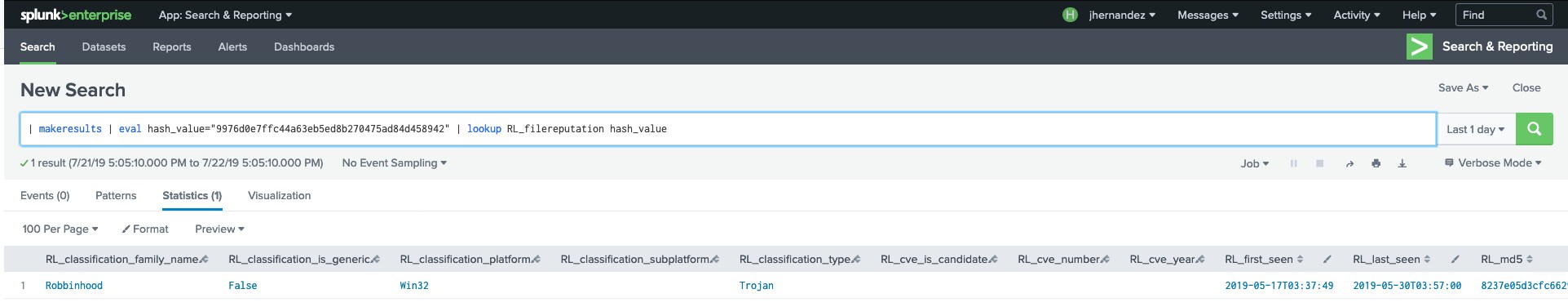
Where hash_value is the md5 hash being looked up, ReversingLabs returns the following fields, which provide more details about this threat, as seen below.
Response
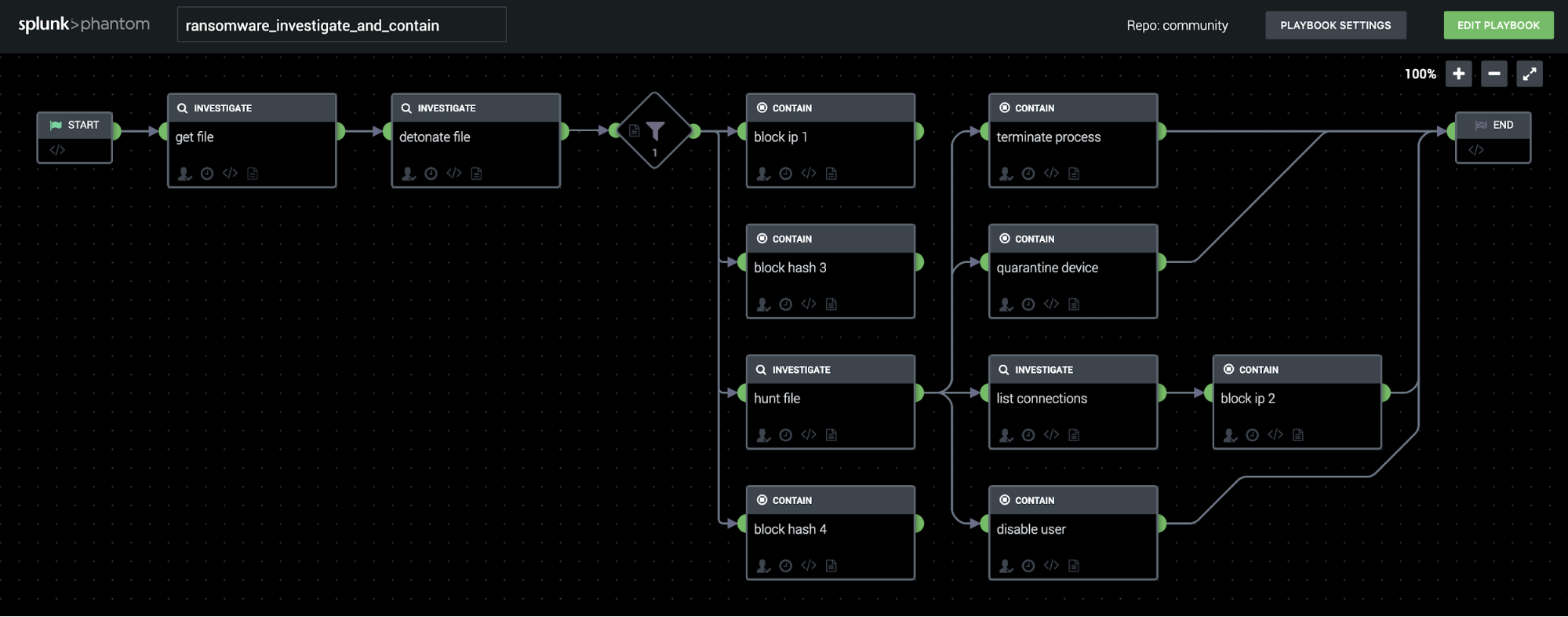
If a ransomware infection has been detected and Splunk Phantom is deployed in the environment, there are a wide range of response options to address different aspects of the threat. Depending on which variant is found, it may be prudent to perform certain simple stop-gap measures such as:
- Using the Windows Remote Management app to copy file, placing any simple text file in the path C:\Windows\temp\pub.key,which may prevent execution of some versions of RobinHood ransomware
- Using an endpoint detection-and-response system to block the hash, preventing new processes from being spawned based on the executable detected in Splunk
- Detecting any domains associated with the ransomware using a reputation service or detonation sandbox and sinkholing or otherwise blocking those domains
- Taking a more drastic approach to prevent lateral movement by using the “quarantine device” action with an endpoint protection system.
The community playbook called “Ransomware Investigate and Contain” shows an example of responding to a ransomware infection using a combination of endpoint response, sandbox detonation, firewall blocking, and Active Directory user blocking. The benefit of using an automated response playbook for this type of situation goes beyond simply saving the time of analysts and incident response teams, because it may also help execute a hash block or IP block quickly enough to save files before they are encrypted or exfiltrated. By using a sandbox detonation or a ReversingLabs file reputation query, playbooks like this can dynamically fetch network indicators and file hashes based on the latest behavior of the ransomware, allowing the response to adapt as more intelligence about the malware is gathered.
Mitigation
The ransomware threat can be mitigated by proactively applying a three-point prevention plan:
- Backups: It is important to have an effective backup strategy. Many affected organizations have been able to skip payment of affected assets and simply restore from backup.
- Updates: Systems that are unpatched and outdated are prime targets of criminals. Organizations must have a patch/update plan in place to mitigate possible attack vectors due to having systems/software out date and unpatched. Operating systems like Microsoft Windows have their own AV/FW defense systems that have updates addressing these types of threats.
- End-user training: Knowledgeable users can spot and prevent phishing attacks and save the organization from being compromised. There are multiple programs and vendors that can help organizations train their users in security. The cost of not doing it is much higher.
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.