ATT&CK-ing the Adversary: Episode 1 - A New Hope
When I first started writing this as an installment of Hunting with Splunk, it started off as a way to inform our readers about this cool thing called MITRE ATT&CK. But as I kept writing and writing, I realized that I started something and now I'm not too sure. So rather than give you what I hoped would be a really good, but long blog post (think The Right Stuff or The Godfather Part II), I would bring you a trilogy instead (hopefully with Ewoks and not Jar-Jar!) This first episode focuses on what MITRE ATT&CK is and the components that make up ATT&CK and how this framework can be used for threat hunting. The second installment walks through applying specific techniques to focus our hunting in Splunk. Finally, the last chapter examines how we can use ATT&CK with security operations and move from hunting to alerting and taking action.
Over the past 18 months, we have provided many examples of how to use Splunk to hunt, whether by using the stats command or the URL Toolbox to help us parse domains. These capabilities are incredibly impactful when conducting our hunt, but how do we characterize our hunt, guide us to things we should hunt and help us keep our focus?
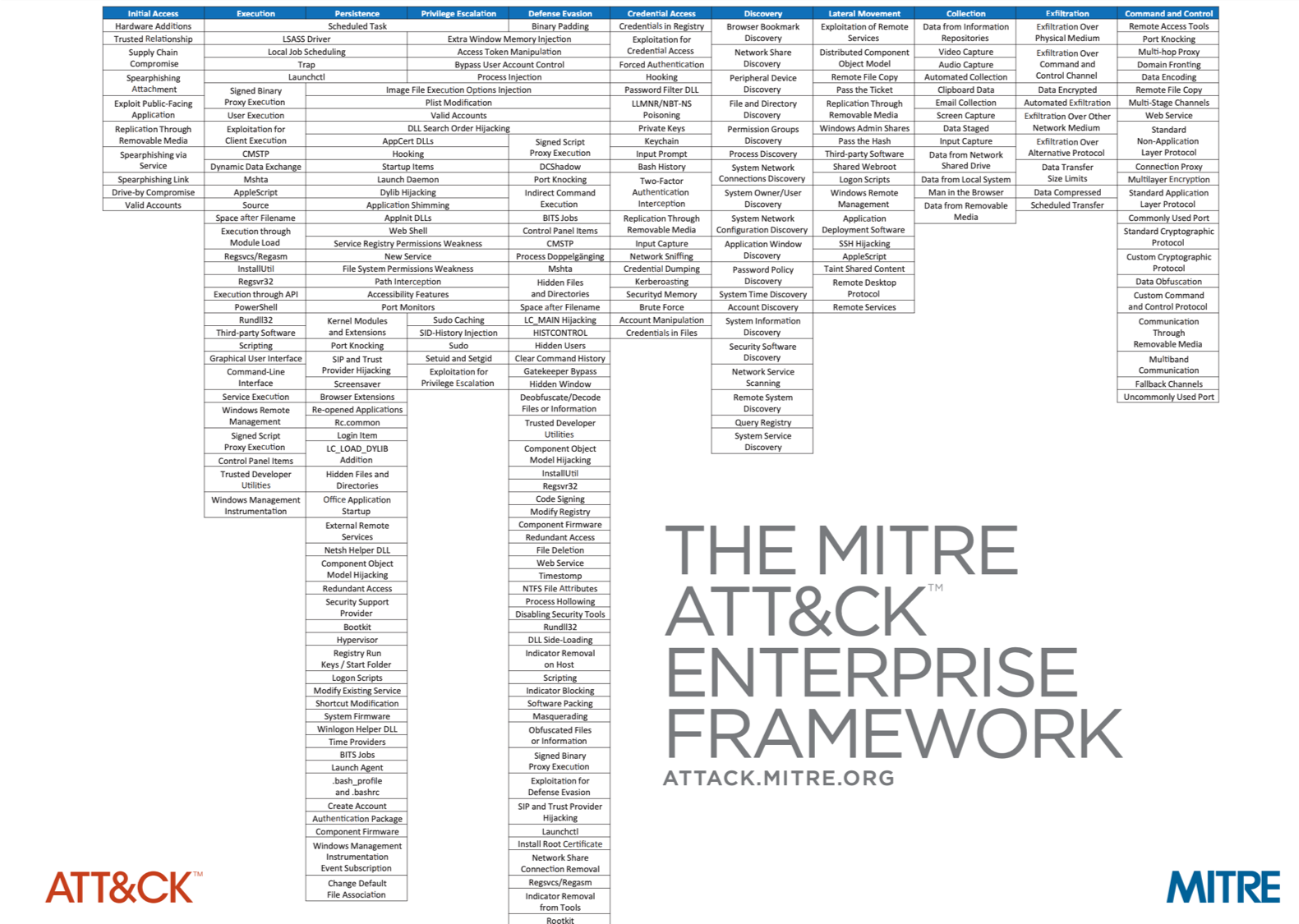
The fine folks at MITRE developed ATT&CK, short for Adversary Tactics, Techniques and Common Knowledge, to address the need to organize and contextualize the multitude of adversary techniques into higher level groupings of tactics, while also cross-referencing these techniques to specific adversaries and software that have been observed using those techniques. Techniques are enumerated for Windows, Linux and macOS and there is a separate matrix for Mobile as well! If that sounds like a lot, that’s because it is! They continue to evolve this with the help of the broader security community adding new techniques that have been observed as well as adversary groups and software.
Adversaries have specific actions that they want to carry out and specific aims they want to achieve. These objectives are going to vary depending on the adversary, just like their targets, but at the end of the day an adversary will use a set of tactics and techniques to achieve their goals. What are tactics and techniques you may ask? Great question. Think of a tactic as a strategy that an adversary is using to achieve their goal. Just like in any other part of life, there are a number of ways to make your strategy successful.
When we apply this to cyber threats, adversaries are likely to use the same techniques over and over because they are well understood and trusted by the adversary, they continually succeed (and if it isn’t broken, don’t fix it!) MITRE’s development of a taxonomy of tactics and techniques and then mapping them to specific adversary groups provides a greater understanding of actions a specific adversary may perform.
For those less familiar with ATT&CK, let me take you through a really quick example to illustrate this relationship.
The tactic of “Lateral Movement (TA0008)”is comprised of many techniques including “Passing the Hash (T1075)”, “Windows Remote Management (T1028)”, and “Remote Desktop Protocol (T1076)”. “Passing the Hash (T1075)” provides a method for an adversary to gain authenticated access to a system without having the cleartext password. One feature of ATT&CK is that it not only illustrates tactics and techniques, but also shows linkages to adversary groups and software. For example, the technique “Passing the Hash (T1075)” is mapped to documented activity from groups like APT1, APT28 and APT29 and is also associated with the following software packages: Cobalt Strike, Mimikatz and Pass-the-Hash Toolkit.
A Rough Illustration of Relationships Between Tactics, Techniques, Software and Adversary Groups
 Unfortunately, I can’t create a multi-dimensional cube in our blogging software, so you get blocks and arrows. My apologies.
Unfortunately, I can’t create a multi-dimensional cube in our blogging software, so you get blocks and arrows. My apologies.
In my rough illustration above, the tactic “Lateral Movement (TA0008)” is in green and the two techniques in grey roll up into that tactic. It is important to note that “Lateral Movement (TA0008)” has 15 techniques today, and some tactics like “Persistence (TA0003)” has over 40 techniques, so for ease of viewing and explanation, I am just showing two techniques.
Each of these techniques has relationships with the software in blue, and with adversary groups in red. Different adversary groups will often use specific software, so the relationship between adversaries and software is indicated with green lines. In our example, APT1 uses Mimikatz as its tool of choice for executing the Pass the Hash technique as part of its operations. Of course, there are many parts to an advanced persistent threat; Mimikatz and Pass the Hash are not the only tool and technique, respectively, that APT1 uses. Depending on what we are focusing on, we can look at ATT&CK from a software, adversary or technique perspective. I hope that helps!
Threat intelligence analysts can also leverage this knowledge to better characterize specific adversaries and connect the dots that their SOC has uncovered. If the threat intelligence team is the first originator of this content, they can also drive these findings back to their SOC to improve analysis! That’s what is really great about ATT&CK; while a lot of the initial efforts were focused on threat intelligence, this enumeration of tactics and techniques can be utilized for threat hunting and operations as well!
When I start planning my hunt, the first thing I want to do is establish a hypothesis and use that as my focus during a hunt. What kinds of hypotheses might I develop? Hypotheses could be as simple as hunting for a specific indicator, like an IP address, file hash or file name though over time I hope that these hunts could be automated into alerts if they are considered high confidence indicators. A slightly more complex hunt could center around looking at volumes of data, like top and bottom talkers in a specific enclave or to a specific database. As I move deeper into my data sets, I want to start focusing hunts on adversary techniques.
David Bianco’s Pyramid of Pain illustrates the challenges and value of hunting TTPs (Tactics, Techniques, and Procedures). From an adversary perspective, it is trivial to change the value of a hash and easy to change an IP within the adversary’s arsenal if one of these indicators is discovered and blocked. It gets much more difficult for the adversary to change their tactics, techniques, and procedures upon being discovered, and not surprisingly, it is difficult to just uncover your adversary’s TTPs. This is where ATT&CK can come into play...
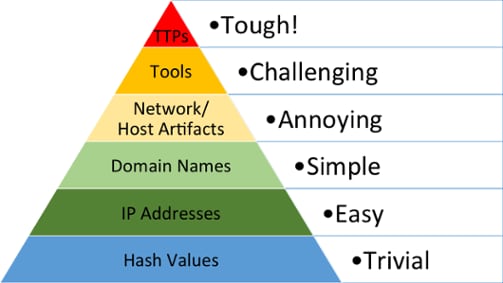
Pyramid of Pain
Using ATT&CK for threat hunting provides the following benefits:
- It allows us to stay focused on a specific technique but flexible enough to uncover ancillary techniques during our hunt.
- The identification of complementary techniques assists us in profiling our adversary based on their use of a specific combination of techniques and software being used.
- Additional hunts can be conducted in the future based on our finding without getting distracted by bright shiny objects that inevitably are uncovered.
Wow, that was a bunch of stuff to cover but I hope it was a helpful primer on what MITRE ATT&CK is. Our next installment will take a look at how we can take a couple of these techniques and apply them directly to our hunt.
Until next time,
Happy Hunting!
----------------------------------------------------
Thanks!
John Stoner
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




