Demo
Security Investigation Online Demo Experience—Malicious Login
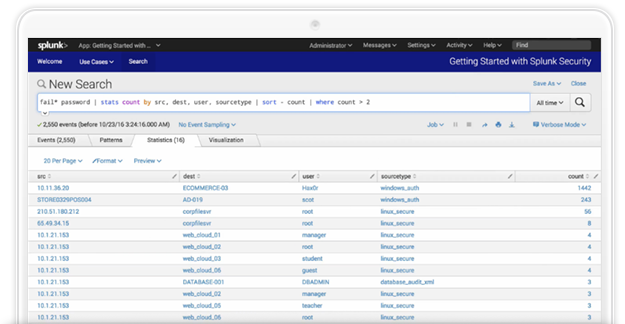
Security incidents occur without warning and can go undetected long enough to pose a serious threat to your business. This Splunk security investigation online experience shows you how to identify potential malicious login activity to determine if deeper investigation is required.
Explore this security investigation use case in our free, online demo environment and learn how to:
- Identify patterns of authentication failures
- Get visibility into malicious access attempts
- Investigate and visualize patterns and sequences to determine how to remediate a threat

