| Capability | Description | Essentials Edition | Premier Edition |
|---|---|---|---|
| SIEM | The market-leading SIEM that provides comprehensive visibility, accurate detections, and operational efficiency across your security operations. | ✓ | ✓ |
| Threat Intelligence | Gain comprehensive coverage, valuable context, and intelligence enrichment to effectively detect, investigate, and respond to threats. Accelerate investigations with integrated threat intelligence enrichment and leverage Cisco Talos threat intelligence at no additional cost. | ✓ | ✓ |
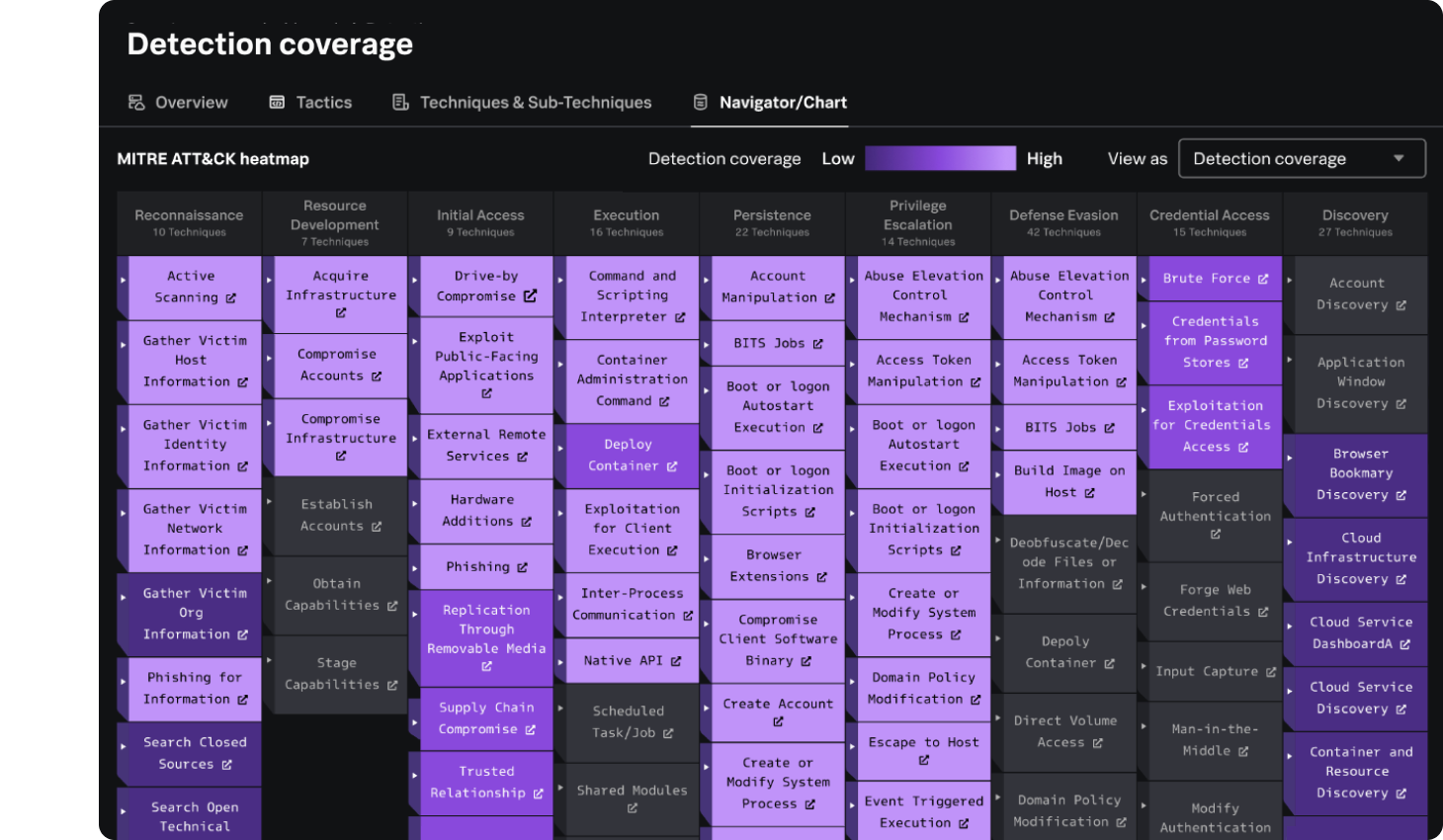
| Detection Studio | As a capability of Splunk Enterprise Security, Detection Studio provides the complete detection lifecycle experience that enables detection engineers to seamlessly plan, develop, test, deploy and monitor detections, thereby improving confidence in detection deployment and enabling faster mean-time-to-detect. | ✓ | ✓ |
| SOAR | Automate security workflows, reducing manual effort, alert fatigue, and response times. Seamlessly integrated with Splunk Enterprise Security, it empowers TDIR automation at scale. | — | ✓ |
| UEBA | UEBA uses behavior-based anomaly detection and machine learning to detect subtle deviations in user and entity behavior, enabling early identification and neutralization of insider threats and advanced threats, such as account misuse, compromised credentials, and lateral movement. | — | ✓ |
analyst report
Unified TDIR business value: Resolve incidents 55% faster
According to IDC, Splunk's unified TDIR platform delivers 304% ROI, 64% faster threat identification, and a 12-month payback, helping organizations accelerate response, cut security costs by $4.89M annually, and boost cyber resilience.

Frequently asked questions
Splunk Enterprise Security (ES) is an integrated threat detection, investigation, and response (TDIR) platform that streamlines security workflows into a unified experience. It integrates capabilities like security information and event management (SIEM), agentic AI and SOAR for automation, UEBA, and AI/ML for improving detection accuracy and response speed.
By bringing these capabilities into a single interface, Enterprise Security reduces inefficiencies, eliminates tool silos, and ensures that SOC teams can detect, investigate, and respond to threats more effectively.
Switching to ES Premier delivers immediate, tangible benefits to current Splunk customers. These include:
- Tool consolidation: Consolidating various security tools into a unified platform for TDIR streamlines workflows and significantly reduces the time and complexity teams face when managing incidents. By integrating disparate tools into a single interface, customers can eliminate context switching, reduce manual steps, and gain a centralized view of threats and alerts.
- Integrated machine-learning powered UEBA: Customers gain deeper insights into anomalous user and entity behavior to identify insider threats, compromised accounts, and advanced methods such as zero-day attacks.
- SOAR capabilities for the entire SOC: ES Premier removes previous limitations on who can use security orchestration, automation, and response (SOAR) — making automation available to all team members — regardless of their role or seniority. This ensures that every SOC role can streamline workflows, enrich alerts, and execute response actions.
By adopting ES Premier now, customers can reduce operational inefficiencies, scale their security operations, and take advantage of the latest AI-driven capabilities.
*Controlled availability where available.
As for today, Enterprise Security currently has two versions of editions that customers can choose from: Essentials and Premier. ES Essentials offers not only the well-known SIEM, but also AI Assistant for Security (AIA), and Detection Studio when available.
Splunk Enterprise Security Essentials is a security information and event management (SIEM) solution that has been a leader in the market for over a decade. Meanwhile, Splunk Enterprise Security Premier extends beyond the capabilities of solely SIEM. ES Premier is a new unified platform for threat detection, investigation, and response that brings together SIEM, UEBA, SOAR, and AI capabilities — all built into a single platform to address today’s rapidly evolving security landscape.
Splunk Enterprise Security Essentials and Premier are available both on-prem and in the cloud.
To ensure teams can hit the ground running, every ES Premier subscription includes education credits. These can be used to build critical expertise in Enterprise Security, identifying insider threats, and mastering security operations.
Additionally, Splunk offers Professional Services to help accelerate implementation of your ES solution and tailor detections, response playbooks, and automated workflows to exact specifications, ensuring the platform better protects your business and provides maximum value.
No. Using Federated Search and Federated Analytics, you can send your data to Amazon S3 or Amazon Security Lake (as well as index them in Splunk) to use your data in the most cost-effective way.