Security Blogs
Latest Articles
template
category
category
security
Ensuring Success with Splunk ITSI - Part 1: Thresholding Basics
Practical step-by-step guidance to configure ITSI to produce accurate and trusted alerts
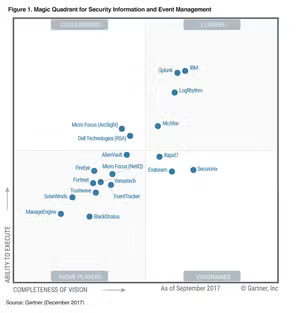
Splunk Named a Leader in Gartner SIEM Magic Quadrant for the Fifth Straight Year
Gartner's 2017 Magic Quadrant for Security Information and Event Management names Splunk a leader for the fifth straight year

What’s Cyber Security Week like for Splunk? it-sa gold!
Two gold awards and a successful it-sa event - that's how Splunk does Cyber Security Week!

What You Need to Know About Boss of the SOC
We introduced a new security activity at .conf2016 called “Boss of the SOC” (or BOTS), born from our belief that learning can be both realistic and fun.

The GDPR: Ready for the wakeup call from your Data Privacy Officer?
How machine data can help organisations prepare for GDPR and support their compliance programmes

What hygiene has to do with security: Infosec17 Recap
In a wrap up of Infosecurity Europe 2017, Matthias Maier shares the topics, trends and big win of the week.

Splunk and Tensorflow for Security: Catching the Fraudster with Behavior Biometrics
Raising the barrier for fraudsters and attackers: how to leverage Splunk and Deep Learning frameworks to discover Behavior Biometrics patterns within user activities

Punycode phishers - All you need to know
Unicode domains can be used for homograph attacks. Learn what they are and how users can be tricked.

Assigning Role Based Permissions in Splunk Enterprise Security
Learn how to add a new role in Enterprise Security and apply capabilities to it