Threat Hunting with Splunk: Hands-on Tutorials for the Active Hunter
At Splunk, you may hear us pontificating on our ponies about how awesome and easy it is to use Splunk to hunt for threats.

Going back to at least a decade, we’ve tried to make it easy — as you’ll see in the resources below — and yet threat hunting is about as easy as telling someone how easy it is to draw an owl. (Hint: it isn’t.) So, that’s why we started writing this series in 2017.
Today, we are doubling-down on our threat hunting capabilities. That's why we're updating this series, one article at a time, verifying that each tutorial is the best resource for some aspect of hunting, all using Splunk.
Want to learn more about threat hunting in general? Keep reading for more information about hunting and the team behind this series, SURGe.
Threat Hunting resources
So, let's make it clear, this entire series is about using Splunk for your threat hunting activities.
Here's some brand new and forever-favorite resources, too, that are about threat hunting with or without Splunk:
- Threat Hunting: Everything To Know About Hunting Cyber Threats
- NEW: PEAK Threat Hunting Framework Series
- Threat Hunting vs Threat Detection: What's The Difference?
- Incident Response is Dead… Long Live Incident Response from long-time friend Scott J. Roberts (Source: Medium, 2015)
- Hunting the Known Unknowns with DNS (.conf2015 Presentation: MP4 & PDF)
- Hunting the Known Unknowns with PowerShell (.conf2016 Presentation: PDF )
Meet the team

- Rapid Response Guides
- Original research like our analysis of ransomware binaries and a macro-level ATT&CK analysis
- Our weekly Coffee Talk with SURGe broadcasts
- Monthly security reading recommendations
- And lots more
Check out all these resources from SURGe and sign up for rapid response alerts.
And now, onto the hunting tutorials!
Tutorials for threat hunting with Splunk
This series will serve as your foundation for hunting with Splunk. (Brand new to Splunk? Explore our SIEM solution, Splunk Enterprise Security: Learn about Splunk ES | Tour Splunk ES)
Each of these articles take a single Splunk search command or hunting concept and break it down to its basic parts. We will help you create a solid base of Splunk knowledge that you can then use in your own environment to hunt for evil. We will cover everything from hypothesis generation to IDS. Splunk commands like stats, eval and lookups will be examined. And have we got queries for you!
- How To Start Threat Hunting: The Beginner's Guide Get started the right way: Hunting in a new environment, tutorial-style
- Using the Lookup Command for Threat Hunting (Lookup Before You Go-Go) Up next: the Lookup command! Compare IOCs or other items of interest against your Splunk dataset
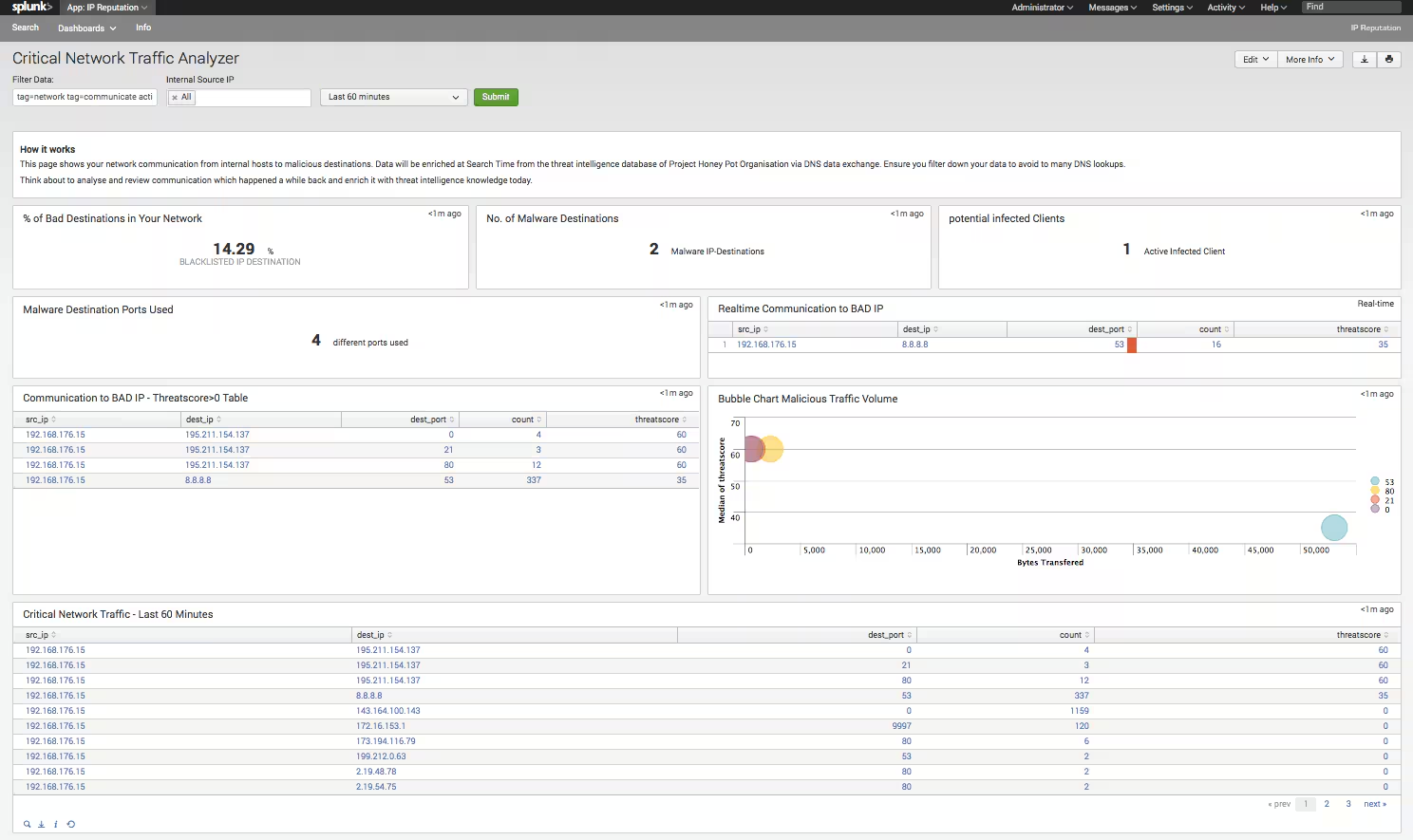
- Splunk Stream for Hunting: Finding Islands in the Stream (of Data) Using Splunk Stream to find malicious activity in your network
- Using Workflow Actions & OSINT for Threat Hunting in Splunk Using Workflow actions and Open Source Intelligence sources
- MetaData > MetaLore: Using the metadata & stats commands Using metadata and tstats to quickly establish situational awareness
- Peeping Through Windows (Logs): Using Sysmon & Windows Event Codes The most valuable places to start hunting in your Windows logs with Sysmon data and events
- Need To Hunt, Stat! Using stats, eventstats & streamstats for Hunting Using the three different stats commands for hunting adversaries in Splunk
- Stat! 3 Must-Have Data Filtering Techniques for Hunting Introducing a set of foundational Splunk threat-hunting techniques that will help you filter data
- Using Regular Expressions (RexEg): It's Not Gibberish Using the rex and regex commands in SPL to rip apart data when you're hunting
- Parsing Domains with URL Toolbox (Just Like House Slytherin) Using the URL Toolbox to break apart URLs and DNS queries into domains, subdomains, TLDs, and more
- Detecting Dubious Domains with Levenshtein, Shannon & URL Toolbox Using the URL Toolbox to analyze Splunk fields for Shannon entropy and Levenshtein distance
- Using eval to Calculate, Appraise, Classify, Estimate & Threat Hunt Using the eval command in Splunk to help modify data (on the fly) and enrich fields
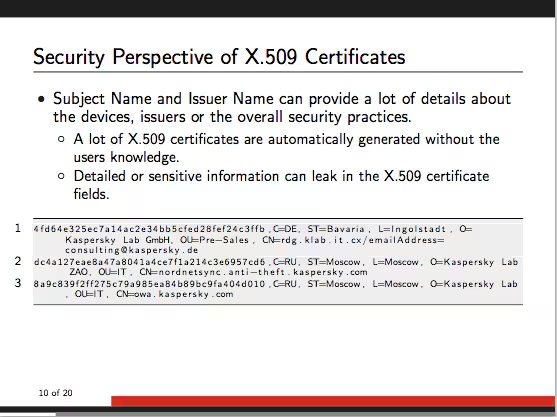
- Threat Hunting with TLS/SSL Certificates Using TLS and SSL certificates to hunt advanced adversaries
- Finding NEW Evil: Detecting New Domains with Splunk Using Splunk (and Splunk Enterprise Security) to find domains that are "new" to your organization
- Hunting with SA-Investigator & Splunk Enterprise Security (SIEM) Using the new SA-Investigator add-on for Splunk Enterprise Security to dig deep into your data models and find the evil lurking within
- Detecting DNS Exfiltration with Splunk: Hunting Your DNS Dragons Using Splunk to "hunt" for malicious DNS behaviour in your network
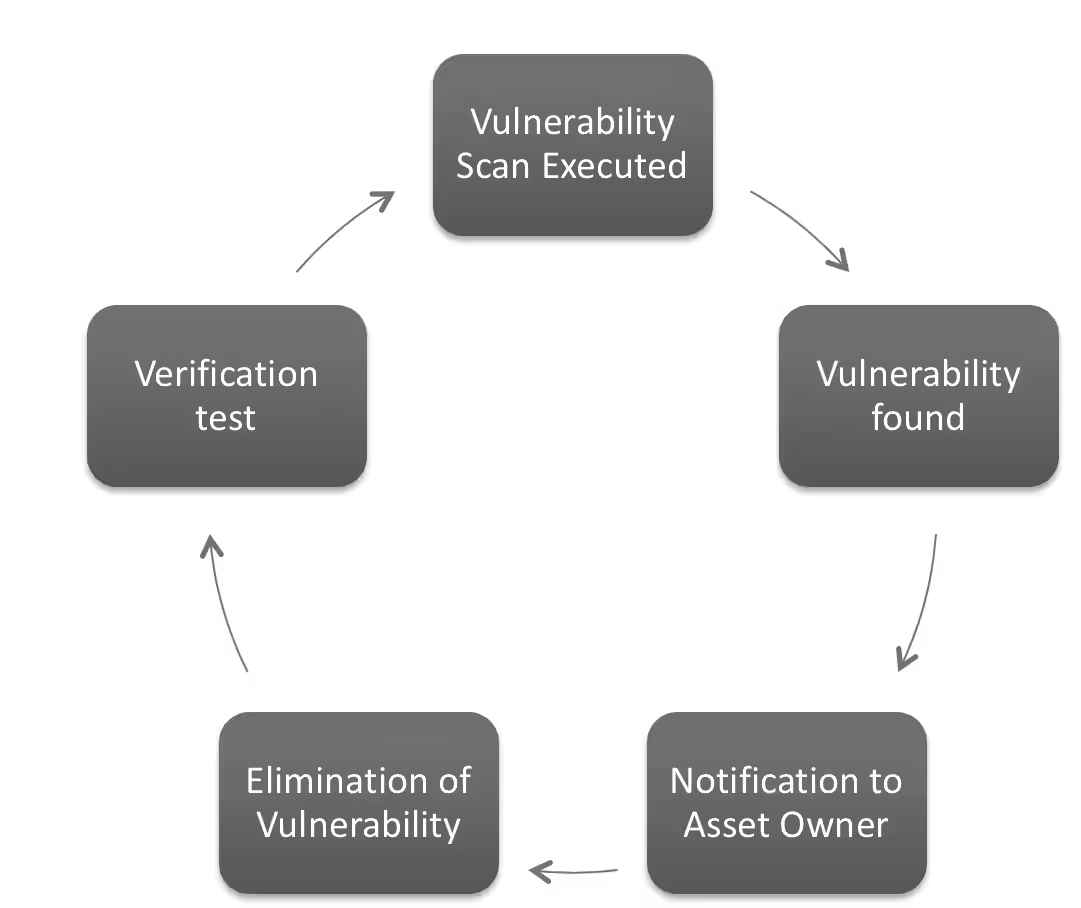
- I Have a Fever, and the Only Cure for It Is More Feedback Providing feedback from hunting into security operations
- The Future is Cloudy with a Chance of Microsoft Office 365 Using Microsoft Office 365 data to hunt in Splunk
- I Azure You, This Will Be Useful Using Azure Active Directory for basic hunting and discovery
- November Spawned an Osquery Hunting through osquery logs
- Detecting Lateral Movement with Splunk: How To Spot the Signs Using Splunk core to identify lateral movement in an organization
- Using CloudTrail Data for Security Operations and Threat Hunting Using AWS CloudTrail as a security logging source and how to hunt in it
- Hunting for Threats in VPCFlows Using VPC data from AWS in Splunk to hunt, hunt, hunt
- Process Hunting with PSTree To make hunting in Splunk better and faster by tracing activities and relationships of a particular process
- No Regrets Using Autoregress Using the autoregression command, which is a centralized streaming command, to calculate a moving average and gather information.
- Detecting & Hunting Named Pipes: A Splunk Tutorial Hunting pipes, the complete guide.
As always, happy hunting!
Related Articles