Navigating NIS2 - Accelerating IT/OT Security in Manufacturing with Splunk, Claroty and AWS
Security Ewald Munz , Sahil GuptaAuthors:
- Ewald Munz, Head of Manufacturing, Automotive and Sustainability EMEA – Splunk/Cisco
- Sahil Gupta, Partner Sales Engineer – Splunk/Cisco
- Gilad Avrashi, Director of Corporate Strategy – Claroty
- Sanjay Mahato, Global Partner Development Specialist Manufacturing - AWS
Manufacturers in 2026 are facing a rapidly evolving landscape where cybersecurity, regulation, and digital transformation intersect. The implementation of NIS2, rising cyber threats, and the growing convergence of IT and OT systems are reshaping how factories operate and protect their assets. Understanding these key challenges is essential for manufacturers aiming to stay compliant, resilient, and competitive in an increasingly connected world.
Three Key Manufacturing Challenges 2026: NIS2 Implementation, Cyber Risks, Growing IT/OT Convergence
Challenge No. 1: NIS2 Implementation
The NIS2 Directive is the EU-wide legislation on cybersecurity. It provides legal measures to boost the overall level of cybersecurity in the EU.

The new directive applies to many manufacturing organizations, not only sectors of high criticality. Key points include the following:
- Strict incidence reporting mandate (24h)
- Personal liability of C-level
- Huge penalties up to €10M
However, many manufacturing companies have delayed tackling this regulation and struggle, also due to the inconsist implementation status by countries. As of now, 21 out of 27 EU Member States have transposed the NIS2 Directive into national law.
NIS2 Implementation Status by Country


Sources: OpenKritis, Ecs-Org
Challenge No. 2: Cyber Risks
Manufacturing is the most attacked industry – five years in a row. The manufacturing sector represented 28% of all cyberattacks in 2025 — the highest percentage of all industries, according to IBM X-Force’s 2026 report.
Exploitation of public-facing applications was the most common way that attackers breached manufacturing systems, accounting for 32% of all observed cases. 16% used valid accounts, and 11% used external remote services, reflecting attackers’ reliance on “exploiting misconfigured or insufficiently secured access points.”
Like the threat landscape itself, the CISO’s role is getting bigger. According to the Splunk CISO Report 2026 - From Risk to Resilience in the AI Era the CISO’s biggest obstacles include sophistication of threat actor capabilities and pace of technology and AI advancements. 78% are concerned about their own liability for security incidents.
Highlighting increasing cyber risks, the World Economic Forum - Global Cybersecurity Outlook 2026 explores how accelerating AI adoption, geopolitical fragmentation and widening cyber inequity are reshaping the global risk landscape. As attacks grow faster, more complex and more unevenly distributed, organizations and governments face rising pressure to adapt amid persistent sovereignty challenges and widening capability gaps.

Source: WEF, Global Cybersecurity Outlook 2026
Challenge No. 3: Growing IT/OT Convergence
Industrial organizations are in the midst of an unprecedented transformation. Smart factories, connected energy grids, water treatment facilities, and logistics networks now depend on a deeply interconnected fabric of Operational Technology (OT), Industrial IoT (IIoT), and enterprise IT infrastructure. This convergence has unlocked remarkable gains in efficiency, automation, and data-driven decision-making.
But there's a flip side.
Every connected PLC, SCADA system, DCS controller, and smart sensor represents a potential entry point for cyber threats. The attack surface has expanded exponentially, and traditional IT-centric security tools were simply never designed to understand the unique protocols, behaviors, and safety requirements of OT environments. The result? Dangerous blind spots at the very intersection where IT meets OT—exactly where adversaries are now focusing their efforts.
The Need for a Risk Reduction Journey
Taking these challenges into account, many manufacturers are worried NIS2 compliance will intervene with their operations by introducing requirements to reduce risk. However, the business cannot pause for compliance – it requires mid-air transformation. A dedicated five step risk reduction journey can leverage modernization as the catalyst to comply with NIS2.

Why a Tri-Party Approach? Why Now?
No single vendor can solve this problem alone. Effective IT/OT cybersecurity and NIS2 compliance demands a combination of deep industrial asset visibility, advanced security analytics, orchestration & automation, and scalable, resilient cloud infrastructure. That's why the collaboration between Splunk, Claroty, and AWS is so powerful—and so timely.

Each partner brings a distinct, best-in-class capability to the table. Together, they form an integrated ecosystem on the abovementioned risk reduction journey.
Claroty — The Eyes and Ears of the Industrial Environment
Claroty xDome is a modular, SaaS-powered industrial cybersecurity platform that provides the foundational OT Security layer required before manufacturers move data from the shopfloor to the cloud.
Within modernization frameworks such as Manufacturing Applications & Technology Modernization (MATM) highlighted below, this layer is non-negotiable because secure visibility, segmentation, and monitoring must exist before enabling cloud connectivity or advanced analytics. xDome focuses on delivering continuous asset visibility, threat detection, and risk reduction across industrial networks, helping organizations meet strict regulatory requirements such as the NIS2 Directive while enabling safe digital transformation.

Source: Claroty
Visibility & Insights forms the foundation, providing comprehensive asset and network discovery enriched with operational context. Building on this base, three core capabilities—Threat Detection, Exposure Management, and Network Protection—work together to systematically reduce operational risk. At the top, Reporting transforms complex technical security data into clear, business-level risk insights for leadership, enabling auditable compliance and informed decision-making. Collectively, these capabilities strengthen regulatory readiness, particularly in meeting NIS2 requirements.
Overall, Claroty xDome serves as the security backbone for industrial environments—protecting critical operations, reducing risk exposure, and ensuring that data moving from the edge to the cloud does so securely, reliably, and in a fully compliant, auditable manner.
AWS — The Cloud-Based Modernization Engine to Drive Manufacturing Applications & Technology Modernization (MATM)
The MATM framework is a layered approach to modernizing manufacturing environments, starting with secure OT foundations, followed by application modernization, data unification, and finally AI-driven business outcomes.
It emphasizes that modernization must occur in sequence, beginning with foundational security and moving upward because legacy, siloed systems cannot support scalable analytics, AI workloads, or regulatory requirements such as NIS2. Ultimately, MATM enables manufacturers to transform isolated OT and IT environments into integrated, cloud-enabled, data-driven operations.

Source: AWS Manufacturing
AWS offers comprehensive MATM solutions designed to transition legacy industrial systems into smart, cloud-native environments. AWS supports application modernization through migration strategies like re-host, re-platform, and re-factor, it enables the Industrial Data Fabric with scalable storage, analytics, and AI services, and it delivers the compute and automation required to drive predictive maintenance, quality analytics, and autonomous operations. In this architecture, AWS acts as the scalable cloud backbone that allows manufacturing data to move securely from the edge to the cloud once prerequisite OT security foundations are in place.
Specifically, how do AWS, Claroty, and Splunk work together to enable this entire MATM stack?
- Claroty delivers the OT Security foundation in Layer 1 - visibility, threat detection, exposure management, and reporting specifically designed for operational technology.
- AWS provides the cloud foundation - the compute, storage, analytics, and AI services that power Layers 2, 3, and 4
- Splunk unifies IT and OT security data in Layer 3 - the Industrial Data Fabric - providing the unified SIEM and security operations platform that correlates events across both domains.
Together, they enable the entire MATM stack from secure foundation through to business outcomes.
Splunk — The Agentic SOC for Unified Resilience
Splunk has been named a Leader in the Gartner® Magic Quadrant™ for Security Information and Event Management (SIEM) for 11 consecutive years (2015–2025), confirming its sustained leadership in threat detection, investigation, and incident response.
Powering the agentic SOC for unified resilience, Splunk unifies security data, analytics, tools, and AI to automate routine tasks, orchestrate workflows, surface complex insights, and proactively mitigate risk.
Splunk redefines security operations by integrating an open data fabric, powerful analytics, cohesive tools, and human-in-the-loop AI into a unified platform. With Splunk, you can:
- Transform the security team from a reactive "firefighting" unit into a proactive, strategic function.
- Build a foundational layer of AI-based risk analysis, combining customer profiles, threat intelligence, and asset data to support autonomous prevention, self-healing, and continuous learning.
- Empower defenders to anticipate future attacks and orchestrate outcomes at machine speed.
- Turn SecOps into a force multiplier that enables business innovation while staying a step ahead of the adversary.

As part of this unified resilience, Splunk helps manufacturing organizations build a powerful, next-generation security concept for their factories with the help of a dedicated OT Security Add On. The Splunk Add-on for OT Security expands existing Splunk Enterprise Security frameworks to improve security visibility in OT environments. It reaches across both carpeted (IT) and concrete (OT) environments to better apply Splunk Enterprise Security to improve threat detection, incident investigation and response.
Existing specialized OT Security vendors such as Claroty are ingested as data sources to allow for holistic visibility across IT and OT environments. Claroty’s OT Security solution xDome works hand in hand with Splunk’s OT Security solution via the integration app on Splunkbase.
Meet the Team at Hannover Messe 2026


Claroty booth on the AWS booth - Hall 15 / Stand D76
Fireside Chat | April 20 | 14.30 - 14.45 | AWS Stage
Forecasting Future Fortifications:
Industrial Insights on OT Resilience and NIS2 in 2026
The session moves beyond the compliance checkbox, showing how industrial organizations use regulatory mandates as a catalyst to reduce O&M costs, protect brand equity, and turn "secure-by-design" into a measurable competitive advantage.
Speakers:
- Gilad Avrashi - Director of Corporate Strategy, Claroty
- Ashtad Engineer - WW Head of Manufacturing, Supply Chain, Sustainability Solutions, AWS
- Ewald Munz - Head of Manufacturing, Automotive and Sustainability EMEA, Splunk/Cisco
Read On
- Recording of the webinar Navigating NIS2 - Accelerating IT/OT Security in Manufacturing - On demand link
- Claroty - Splunk Integration Brief
Related Articles
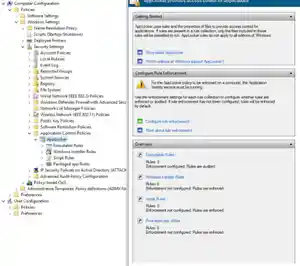
Deploy, Test, Monitor: Mastering Microsoft AppLocker, Part 1

Unveiling Splunk UBA 5.3: Power and Precision in One Package
