Splunk Light: An Introduction and Beginner's Guide
Splunk Light was a version of Splunk’s flagship log search and analysis software that launched in 2015, designed specifically for small IT environments. Splunk Light enabled users to gather and correlate date from all types of sources, formats, and locations. In addition to logfile search and analysis, Splunk Light’s alerts and dashboards helped users get started with critical IT monitoring & observability features quickly and easily.
If you were thinking about trying Splunk Light, you can get all of the benefits of that platform in Splunk Enterprise or Splunk Cloud (depending on your deployment preference).
- Learn more about Splunk Enterprise
- Start your Free Splunk Enterprise Trial
- Learn more about Splunk Cloud Platform
- Start your Free Splunk Cloud Platform Trial
Splunk Light End-of-Life (EoL)
In March 2020, it was announced that Splunk Light and Splunk Light Cloud would reach End-of-Sale on May 1, 2020 and eventually would reach End-of-Support and End-of-Life. Customers of Splunk Light and Splunk Light Cloud have the option to migrate to Splunk Enterprise.
Per the announcement, the End-of-Life Timetable was as follows:
- October 21, 2019: New major releases of Splunk Light stopped.
- April 24, 2020: Splunk Light 7.1.x End-of-Support via official support policy.
- May 1, 2020: Splunk Light and Splunk Light Cloud End-of-Sale. No new sales or renewals on Splunk Light or Splunk Light Cloud are allowed. Migrations from Splunk Light to Splunk Enterprise can begin.
- October 2, 2020: Splunk Light 7.2.x End-of-Support via official support policy.
- April 30, 2021: Migration from Splunk Light to Splunk Enterprise no longer supported. All Splunk Light support and maintenance purchased before May 1, 2020 by perpetual customers expires.
- June 4, 2021: End-of-Life for Splunk Light and Splunk Light Cloud.
Splunk Light vs Splunk Light Cloud
In September of 2015, the cloud service (SaaS) version of Splunk Light was made available. This deployment option included the same benefits of the original on-premises version of Splunk Light, but without the headaches of purchasing, setting up, and maintaining a server. As mentioned previously, both Splunk Light and Splunk Light Cloud were officially End-of-Life’d in June 2021.
Splunk Light vs Splunk Light Free
There were a variety of differences between Splunk Light and Splunk Light Free. This table elaborates on the differences.
Splunk Light vs Splunk Enterprise
Differences between Splunk Light and Splunk Enterprise included:
Related Articles

Intelligent Applications Explained

Open Source vs. Closed Source Software

Secure By Design: What Makes Software SbD

Information Retrieval & Intelligence: How It Works for AI

Adversarial Machine Learning & Attacks on AIs
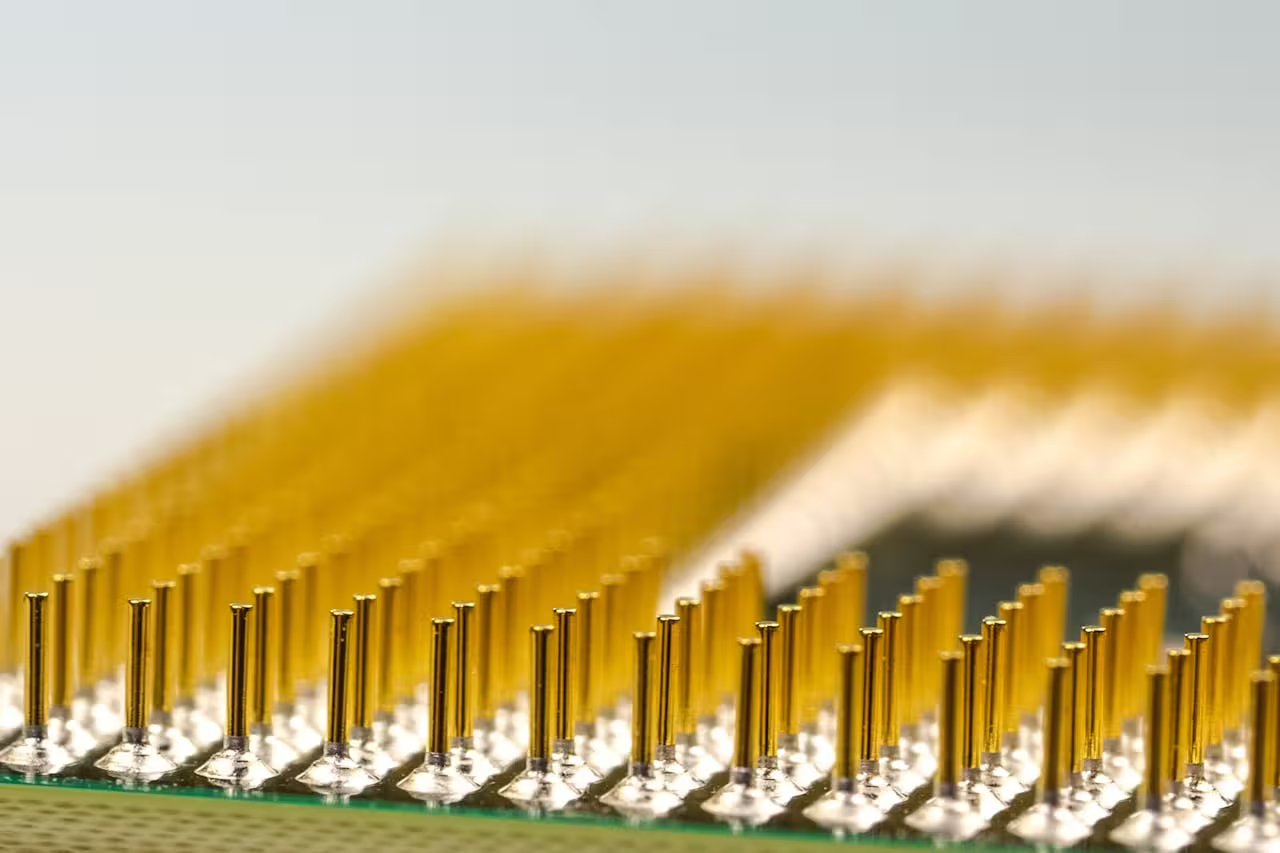
CPUs vs GPUs: Comparing Compute Power

Why Effective Data Management Matters: Key Principles & Best Practices

Executive Order 14028: Improving U.S. Cybersecurity
