Learn Blogs
Latest Articles
template
category
category
learn
hideCategoryPill
true

What Is Predictive Maintenance? Types, Uses Cases, and How It Works
Predictive maintenance is a data-driven strategy to minimize downtime by scheduling maintenance only when needed. Learn more here.

Events, Alert, and Incidents: What’s The Difference? How Do They Relate?
Effectively managing events and alerts is essential for preventing or quickly resolving incidents, whether it’s a sudden service outage or an ongoing cyberattack.

Introduction to Reinforcement Learning
Reinforcement learning is at the core of some of the most prominent AI breakthroughs in the last decade. Learn how it works here.

Responsible AI: What It Means & How To Achieve It
Responsible AI addresses many risks and concerns around AI systems, which may lead to the best possible outcomes for AI and modern society.

The Data Analyst Role Explained: Responsibilities, Skills & Outlook
Learn all about the role of Data Analyst, including the skills, responsibilities, and expectations, plus experience levels across organizations of all sizes.
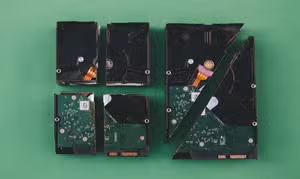
Data Backup Strategies: The Ultimate Guide
Discover smart data backup strategies to prevent loss, ensure recovery, and protect your business with tools, cloud, AI, and modern best practices.

The Theory of Constraints: The Complete Guide to Constraint Theory
Theory of Constraints (TOC) is a management concept that tries to leverage any bottlenecks in a system in order to improve overall system performance.

Concurrency in Programming and Computer Science: The Complete Guide
Learn how concurrency powers efficient multitasking in modern systems, from single-core CPUs to distributed systems.

Database Monitoring: The Complete Guide
In this blog post, we'll take a look at the important role of database performance monitoring.