Learn Blogs
Latest Articles
template
category
category
learn
hideCategoryPill
true

Denial-of-Service Attacks: History, Techniques & Prevention
DoS attacks have a long history, but they’re also predicted to get worse in 2023. Find out the many ways they work and learn to prevent them in the first place.

Encryption Explained: At Rest, In Transit & End-To-End Encryption
Humans have encrypted messages for millennia. Today it’s essentially part of daily life. Understand how it works — and decide if you need end-to-end encryption.

What is DevOps Automation?
Automation is essential to DevOps — but it’s not easy. This guide details how to automate DevOps and the best tools for the job so you can succeed in no time!
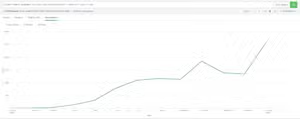
Using Splunk for SEO Log File Analysis
This blog post will showcase just a few of the ways we’re using Splunk to improve our own technical SEO.

CMDBs Explained: Configuration Management Databases
Meant to provide visibility into all IT assets, CMDBs are routinely underutilized. Learn how to plan, implement and maintain a CMDB to maximize business value.

What is ETL?
Strengthen your data foundation by knowing ETL. Short for Extract, Transform, Load, the ETL process is vital for turning all that data into business value.

What is Ethical Hacking?
Ethical hacking is one way to understand vulnerabilities within your system. Learn how to hack ethically, get trained and see how hacking supports security.

Logs vs Metrics: Pros, Cons & When to Use Which
In the metrics vs logs debate, we come down firmly in the “use both, smartly” camp. See how logs and metrics create a complementary observability foundation.

Splunk MINT: A Complete Introduction
Looking for Splunk MINT? This blog post explains in detail what Splunk MINT was, what happened to Splunk MINT, and much more.