Hemant Seth's Blog Posts
Hemant is a Principal Product Manager at Splunk, leading the Kubernetes Monitoring offering within Splunk Observability Cloud. Prior to this role, he focused on Splunk Observability Platform administration, including identity management and license usage. Hemant brings over a decade of experience in the observability domain and holds a Master’s degree in Electrical Engineering with a specialization in Telecommunications.
Display Mode
Paginated
Filter
Author
Author URL
Limit
6
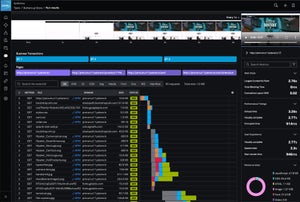
Announcing the General Availability of Synthetic Monitoring Within Splunk Observability
Splunk now offers fully integrated synthetic monitoring within Observability, helping IT and engineering teams proactively detect and resolve performance problems before they reach customers, with full visibility from the end user experience, through backend service performance

Postcard From .conf22: Customers Inspire Our Latest Release
Customer contributions inspire the latest release of Splunk Enterprise 9.0 and the Splunk Cloud Platform.

Staff Picks for Splunk Security Reading July 2022
Welcome to the Splunk staff picks blog. Each month, Splunk security experts curate a list of presentations, whitepapers, and customer case studies that we feel are worth a read.

Welcome to the Future of Data Search & Exploration
Introducing the new SPL2 Search Experience for Splunk Cloud, accelerating the data-to-insight workflow, and bringing the power of Splunk to everyone – learn more here.

SPL With No Joins
You always join on time with Splunk - so you don't need to run explicit joins with your records.

ML Detection of Risky Command Exploit
Discover how to use machine learning algorithms to develop methods for detecting misuse or abuse of risky SPL commands to further pinpoint a true security threat.