The Evolution of the SOC: Moving from Reactive to Agentic with Enterprise Security at RSAC 2026
Security Michael MartiKey takeaways
- Modern security teams are overwhelmed by too many tools and growing AI-driven threats, making the traditional reactive SOC model unsustainable.
- New updates to Splunk Enterprise Security introduce unified visibility, smarter risk prioritization, and AI agents that automate time-consuming security tasks.
- These innovations help organizations shift to an “Agentic SOC,” where humans and AI work together to detect threats faster, reduce burnout, and strengthen overall security.
The modern Security Operations Center (SOC) is at a breaking point. Between the fatigue caused by tool sprawl, the chronic burnout of expert talent, and the proliferation of shadow IT, the traditional reactive model is no longer sustainable. To keep pace with AI-driven threats and more sophisticated APTs, security organizations must transition from manual, siloed workflows to an "Agentic SOC."
Today at RSAC 2026, we announced a series of major advancements within Splunk Enterprise Security (ES) designed to bridge this gap—further reinforcing Splunk ES as the AI-Powered, SecOps platform.
Scaling Operations with High-Fidelity Visibility
The foundation of a secure environment is knowing what you have and ensuring your detections are effective. With Detection Studio and our latest releases of Federated Search, we’re allowing teams to have control over their detections and visibility across their estate.
- Detection Studio: We are moving beyond the fragmented detection lifecycle many security teams struggle with today. Detection Studio provides a unified workspace for detection engineers to plan, develop, test, deploy, and monitor detections. By mapping coverage against the MITRE ATT&CK framework, teams can identify data gaps and validate detection quality in real-time, significantly reducing the mean-time-to-detect (MTTD).
- Federated Search: The announced updates to Federated Search further empower SecOps teams to gain comprehensive visibility across distributed data sources, including cloud lakes and SaaS, without the cost or complexity of upfront ingestion. Federated Search now allows security teams to search and investigate data across S3, Iceberg, and other stores, without ingesting it into Splunk. This reduces costs and accelerates time-to-insight while maintaining compliance with flexible performance trade-offs.

Streamline Detection and Response To Focus on What Matters With Exposure Analytics
Most organizations are flying blind regarding their attack surface—you cannot protect what you cannot see. New to Splunk ES, Exposure Analytics helps to provide trusted visibility across your environment.
- Continuous Discovery: Exposure Analytics automatically discovers assets and users across the environment. By leveraging data already being ingested, it provides a “Security Truth Layer" without the need for additional agents or tools.
- Contextual Prioritization: By mapping relationships between assets and identities, Exposure Analytics provides context-rich Entity Risk Scores that provide transparency and near real-time insights on entities. This allows analysts to move away from manual research and focus on high-priority investigations that actually impact the attack surface.

The Rise of AI Agents: Moving at Machine Speed
The "Agentic SOC" is defined by the transition from human-led manual tasks to AI-augmented collaboration, and our AI-Powered SecOps platform is simplifying the TDIR experience with our new specialized AI agents. Soon available in ES, these agents are designed to handle the heavy lifting, freeing human experts for high-value defense and strategic initiatives.
- Detection Builder Agent: This agent helps SOC teams go from detection hypothesis to production in minutes with accuracy—allowing teams to quickly import, tune, and tag detections.
- SOP Agent: The SOP Agent helps by importing security standard operating procedures (SOPs) into Splunk ES response plans using multi-modal LLMs. Other agents can then execute these SOPs as defined by the SOC, greatly accelerating repeatable processes.
- Triage Agent: This agent helps to autonomously enrich, prioritize, and explain alerts, greatly reducing the fatigue put on analysts.
- Malware Threat Reversing Agent: This agent gives analysts instant insight into malware threats, providing summaries and step-by-step breakdowns of malicious scripts.
- Guided Response Agent: The Guided Response Agent automatically executes response actions (such as quarantining) based on your SOC’s standard operating procedures.
- Automation Builder Agent: The agent helps translate natural language into functional, tested SOAR playbooks aligned to your specific processes and use cases. This can significantly accelerate automation across the SOC team and support development of new workflows.

Transforming from a Reactive SOC to the Agentic SOC
Shifting to an Agentic SOC addresses commonly growing pain points that security leaders are faced with today:
- Detection Confidence: Detection Studio eliminates data gaps and provides automatic validation of detection quality, ensuring that security controls are effective against evolving threats.
- Zero-Cost Visibility: Exposure Analytics turns existing data into an inventory of the attack surface, replacing manual, expensive asset management solutions.
- Slash Investigation Time at Machine Speed: By providing SOC teams our new AI agents that shoulder the burden of time-intensive tasks and processes, users can greatly improve their MTTR, allowing more time to focus on defending against sophisticated threats that need an analyst, as well as provide time to work on efforts that strengthen the SOC.
The transition to an Agentic SOC is not just about adopting new tools; it is about changing the fundamental operating model of the security team. By integrating clean data via Exposure Analytics and automated intelligence via our AI agents, Splunk ES is enabling SOCs to move at the speed of the threats they face.
We invite you to explore these capabilities and features with us while at RSAC 2026 so that you can see them in action and discuss with our experts on how your organization can begin its transition to an Agentic SOC with Splunk Enterprise Security.
Unable to see us at RSAC? Check out our Splunk ES Premier product tour or watch our Demo Day: End SOC analyst fatigue with the reimagined Splunk Enterprise Security to learn more about how we’re evolving the SOC from being reactive to agentic.
Related Articles

Enhancing SIEM Events with Automated Threat Analysis of URLs
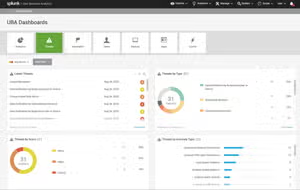
Elevating Security Intelligence with Splunk UBA's Machine Learning Models
