Security Blogs
Latest Articles
template
category
category
security
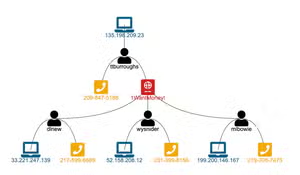
Visual Link Analysis with Splunk: Part 2 - The Visual Part
Using Splunk for link analysis - part 2 covering visualizations of linked data.
Cybersecurity Today: Alice in Wonderland Meets the Matrix & Total Recall
The scale of cyber attacks and the complexity of networks exacerbate the situation. Operators face three significant challenges: an IT security ecosystem that is fragmented and in flux, users that are both human and machine, and multiple threats with varying levels of severity and sophistication.

Detecting the Sudo Baron Samedit Vulnerability and Attack
Looking for ways to detect and protect against the SUDO Baron Samedit vulnerability (CVE-2021-3156)? Look no further. In this blog we tell you how to proactively detect vulnerable servers using Splunk and also to detect malicious folks who are attempting to exploit this vulnerability for nefarious outcomes!

TruSTAR Enclave: Not Your Grandpa’s 'Trusted Circle'
TruSTAR’s Enclave technology is the most advanced cloud-based governance engine for enterprise cyber intelligence – read on to discover how it has evolved to meet the needs of integration, automation and intelligence sharing.

Visual Link Analysis with Splunk: Part 1 - Data Reduction
Part 1 of a multi-part series exploring ways to use Splunk for link analysis. This blog focuses on data reduction.

Splunk SOAR Playbooks: Finding and Disabling Inactive Users on AWS
Discover how to add an additional layer of security in AWS with Splunk Phantom by scheduling a playbook to search for inactive users and activating another playbook to disable problem user accounts.

Macros, We Don’t Need No Stinking Macros! — Featuring the New Microsoft O365 Email Add-On
Using Microsoft O365 for your emails? Take a look at the new Microsoft O365 Email Add-on for Splunk to start getting in-depth security and non security data from your emails today.

The 10 Essential Capabilities of a Best-of-Breed SOAR
Security orchestration, automation and response (SOAR) tools are here to stay, do you have the best-of-breed SOAR in your security stack?

Yes, Virginia, There is a -Santa Claus- Way to Detect Unemployment Fraud
Fraud rates for Unemployment Insurance Benefits (UIB) and Pandemic Unemployment Assistance (PUA) are out of control. Use these detections to start detecting unemployment fraud now.