Security Blogs
Latest Articles
template
category
category
security

Splunk BOTS 4.0: A New Hope
From the basics, to new data, to registration information, discover all you need to know about Splunk BOTS 4.0 at .conf19.
Which of Gartner’s 2019 Top 7 Security and Risk Management Trends Are Impacting Your Business? - Part II
Part 2 of our 3-part blog series, in which we take a closer look into Gartner Security and Risk Trends 2019 and give you suggestions on how to address them.
Which of Gartner’s 2019 Top 7 Security and Risk Management Trends Are Impacting Your Business? - Part III
Last and final part of our 3-part blog series in which we review Gartner's Security and Risk Trends 2019 and give advise on how to tackle them.
Which of Gartner’s 2019 Top 7 Security and Risk Management Trends Are Impacting Your Business?
In this 3-part series, we take a closer look into Gartner's trends and share how you can address these issues.

New: Machine Learning in Splunk Enterprise Security Content Update
Use machine learning techniques to identify outliers in security-related data with a new probability-density function algorithm in Splunk's Machine Learning Toolkit (MLTK)

Monitor for, Investigate, and Respond to Phishing Payloads with Splunk Enterprise Security Content Update
Detect, investigate, and defend signs of phishing payloads in your environment with Splunk Enterprise Security Content Update (ESCU)

Boss of the SOC (BOTS) Advanced APT Hunting Companion App: Now Available on Splunkbase
If you want to learn more about threat hunting with Splunk, this app in conjunction with the BOTSv2 data set is just the answer!
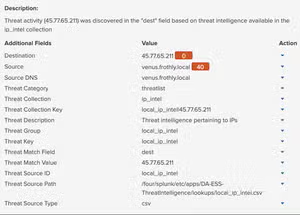
Threat Intel and Splunk Enterprise Security Part 2 - Adding Local Intel to Enterprise Security
Splunker John Stoner shares a walkthrough for how to add local threat intelligence into Splunk Enterprise Security

Boss of the SOC 2.0 Dataset, Questions and Answers Open-Sourced and Ready for Download
You asked, we delivered – Boss of the SOC 2.0 has been open sourced, including dataset, questions, answers and even a scoring server update!