Latest Articles
displayMode
paginated
category
Security
showImagesOnMobile
false

Security
2 Minute Read
Staff Picks for Splunk Security Reading June 2024
Welcome to the June Splunk staff picks blog, featuring a list of presentations, whitepapers, and customer case studies that our Splunk Security experts feel are worth a read.
Security
8 Minute Read
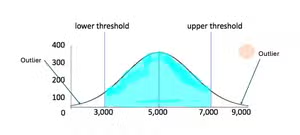
The Geometry of Fraud Detection
Splunker Nimish Doshi shares statistical ways to find outliers and visualizes what they would look like if using virtual area or virtual volume as geometric representations to find them.

Security
4 Minute Read
Zipf's Law and Fraud Detection
Splunker Nimish Doshi breaks down Zipf’s Law to look for possible indicators of fraud.

Security
4 Minute Read
Safe Passage: Seamless Transition Path for IBM QRadar Customers
The SOC is where it all goes down and where dedicated SecOps teams work tirelessly to protect every digital corner of an organization.

Security
15 Minute Read
LNK or Swim: Analysis & Simulation of Recent LNK Phishing
LNK files are a common starting point for many phishing campaigns. Read on to strengthen your defenses against these LNK file phishing attacks.

Security
5 Minute Read
Reduce False Alerts – Automatically!
Splunker Xiao Lin explains the 'False Positive Suppression Model,' now in the UBA tool.
Security
11 Minute Read
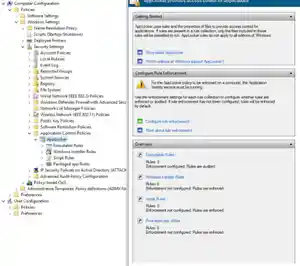
Deploy, Test, Monitor: Mastering Microsoft AppLocker, Part 1
The Splunk Threat Research Team provides a comprehensive overview of AppLocker and guidance for getting started with AppLocker policies

Security
10 Minute Read
Deploy, Test, Monitor: Mastering Microsoft AppLocker, Part 2
Leverage the power of Splunk to ingest, visualize, and analyze AppLocker events, enabling you to gain valuable insights and strengthen your organization's security posture.
Security
6 Minute Read
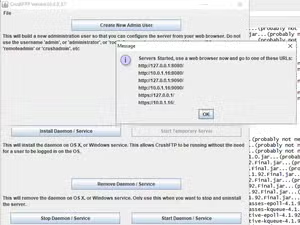
Security Insights: Detecting CVE-2024-4040 Exploitation in CrushFTP
The Splunk Threat Research Team explores how Splunk can help you identify and investigate CVE-2024-4040 exploitation in your CrushFTP environment.