Latest Articles
displayMode
paginated
category
Security
showImagesOnMobile
false

Security
4 Minute Read
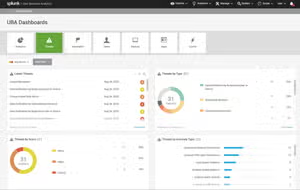
UEBA Superpowers: Enhance Security Visibility with Rich Insights to Take Rapid Action Against Threats
Splunk UBA illuminates hidden corners of your org's digital ecosystem, providing unparalleled visibility into behaviors and patterns that define the network's pulse.

Security
4 Minute Read
Detecting Lateral Movement with Splunk: How To Spot the Signs
Identifying lateral movement is so important, and it sure isn't easy. Using Splunk makes it a lot easier, and we'll show you how in this tutorial.

Security
3 Minute Read
Staff Picks for Splunk Security Reading March 2024
Welcome to the March 2024 Splunk staff picks, featuring a curated list of presentations, whitepapers, and customer case studies that we feel are worth a read.

Security
6 Minute Read
UEBA Superpowers: Detect and Eliminate Advanced Threats with Machine Learning
Splunk User Behavior Analytics (UBA) detects advanced attacks and insider threats with unsupervised machine learning.

Security
6 Minute Read
Level Up Your Security Data Journey and MITRE ATT&CK Benchmarking with Splunk Security Essentials
Announcing the release of Splunk Security Essentials version 3.8.0, which adds maturity journey and benchmarking.

Security
5 Minute Read
Process Hunting with PSTree
This tutorial shows how to use the pstree command & app to help you look through all the processes you have to investigate.
Security
4 Minute Read
Elevating Security Intelligence with Splunk UBA's Machine Learning Models
Splunk UBA uses machine learning to detect evolving threats beyond rule-based approaches in SOC operations, tackling overwhelming event volumes.

Security
2 Minute Read
Enhancing SIEM Events with Automated Threat Analysis of URLs
Splunk debuts Add-on & App for Splunk Attack Analyzer v1.1, elevating security ops via automated URL threat analysis in Splunk ES.

Security
7 Minute Read
Detecting New Domains in Splunk (Finding New Evil)
Ready to find "new" domains that may be naughty? We'll walk you through how to use Splunk & Splunk Enterprise Security to do that: get the full story here!