
Digital Resilience Pays Off
Download this e-book to learn about the role of Digital Resilience across enterprises.
No, thank you! That’s what Splunk would say if it could talk. Dates and times come in many shapes and sizes, so much so I get worried sometimes reading expiration dates on food. Is that the month or the year?? Consider these formats for the same date/time:
January 10, 2010 02:10:00
01/10/2010:14:10:00
10 Jan 2010 02:10.00
01-10-10-14-10-00
… and on and on
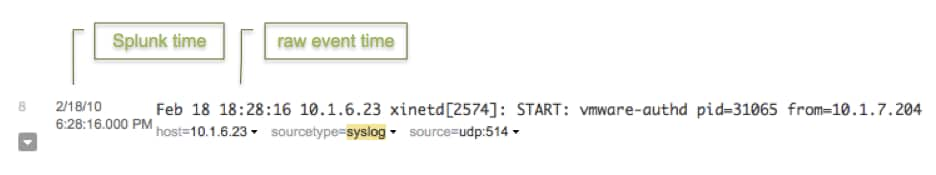
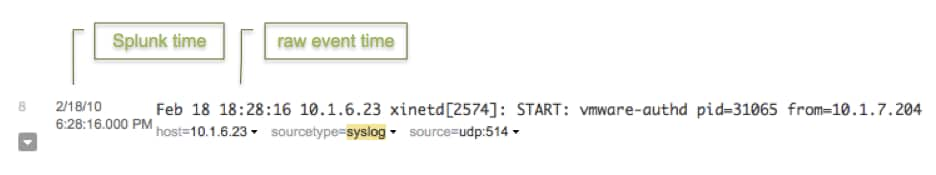
Splunk has many default rules in place to recognize all sorts of date/time stamps. In most cases, Splunk will automatically detect the right date/time in the event or the file name and normalize it to the Splunk server time. At the least, when adding a new data input, please ensure the date/time Splunk extracts matches the event date/time. The Splunk date/time is displayed to the left of the raw event in dark gray when viewing events in the search view.
However, if Splunk didn’t have to make an educated guess about the date/time, it can index data that much faster. Configuring explicit rules for date/time extraction can make Splunk more efficient. Additionally, while Splunk is quite good at recognizing date/times without any help, it’s impossible to have the default rules cover all possible formats, in which case you will need to configure timestamping rules.
To do so, use these parameters in props.conf:
[mydatasource] TIME_PREFIX = <regular expression> TIME_FORMAT = <strptime-style format> MAX_TIMESTAMP_LOOKAHEAD = <integer>
These options and examples are documented in $SPLUNK_HOME/etc/system/README/props.conf.spec and here.
Minimally, if you know the date/time appears at the beginning of the event, say in the first 32 characters, then reducing the MAX_TIMESTAMP_LOOKAHEAD will prevent Splunk from reading further into the event than it really needs to in order to find the date and time.
You can also reduce the havoc wrought by the very ugly problems of having events dated erroneously in the distant past or even in the future by tuning these settings, also in props.conf:
MAX_DAYS_AGO = <integer> ∗ Specifies the maximum number of days past, from the current date, for an extracted date to be valid. MAX_DAYS_HENCE = <integer> ∗ Specifies the maximum number of days in the future, from the current date, for an extracted date to be valid.
The essential unit of correlation in Splunk is time. To make the best use of a time series search engine, getting the timestamping correct is a must, and doing some basic date/time config can also make for a leaner, greener Splunk.
----------------------------------------------------
Thanks!
Vi Ly
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.