
Digital Resilience Pays Off
Download this e-book to learn about the role of Digital Resilience across enterprises.
Security practitioners – take notice! You can now use the power of data science and machine learning across the entire security operations and security intelligence workflow.
Updated 4/19/16
Today, we announced the general availability of Splunk® User Behavior Analytics 2.2 (UBA) and Splunk Enterprise Security 4.1 (ES) which brings significant innovations of Splunk UBA to Splunk ES as well as introduces significant enhancements to both solutions.
Behavioral Analytics in SIEM Workflow
The Splunk ES now uses machine learning detected anomalies data to optimize routine SIEM tasks, reduce complexity, speeding up the ability to detect, investigate and respond to real threats and attacks. Unlike other security solutions that may include analytics based on statistical anomaly detection, Splunk combines both ML anomaly detection and criteria-based correlation together into a single advanced analytics SIEM security solution.
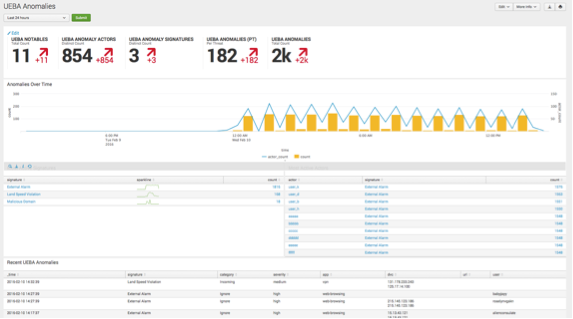
Splunk UBA detected anomalies are now available as a sourcetype within Splunk ES and can be used for multiple SIEM workflows to deter and resolve threats quicker and with greater precision.
Enhanced insider threat and cyber attack detection using Splunk UBA
Custom Threat Modeling Framework
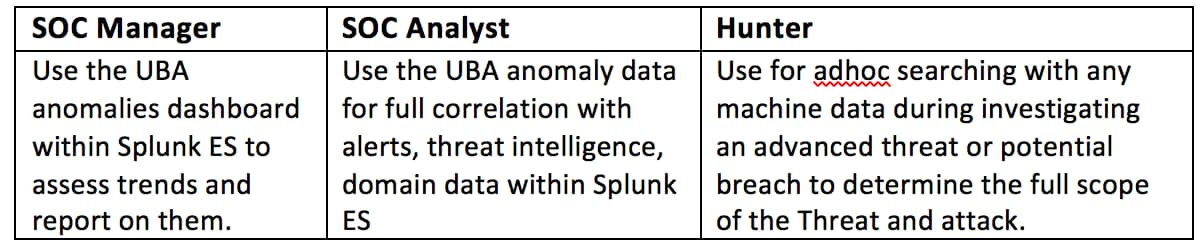
 Splunk UBA now enables customers’ to create custom threat scenarios on top of anomalies detected by machine learning. This helps with real-time threat detection and can be leveraged to detect threats on historical data. With over sixty anomaly classifications, analysts can create many combinations and permutations of threat detection scenarios along with automated threat detection.
Splunk UBA now enables customers’ to create custom threat scenarios on top of anomalies detected by machine learning. This helps with real-time threat detection and can be leveraged to detect threats on historical data. With over sixty anomaly classifications, analysts can create many combinations and permutations of threat detection scenarios along with automated threat detection.
Improved Precision and Prioritization of Threats
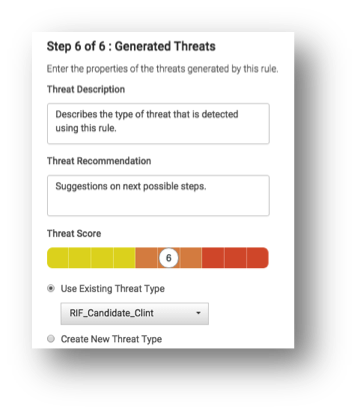
Splunk UBA has expanded support for new data source types (end-point products, network security solutions, and applications) that not only improve detection capability, but also helps with prioritization of alerts and further reduce false positives. The latest coverage involves suspicious behavior for data access and data exfiltration using physical media.
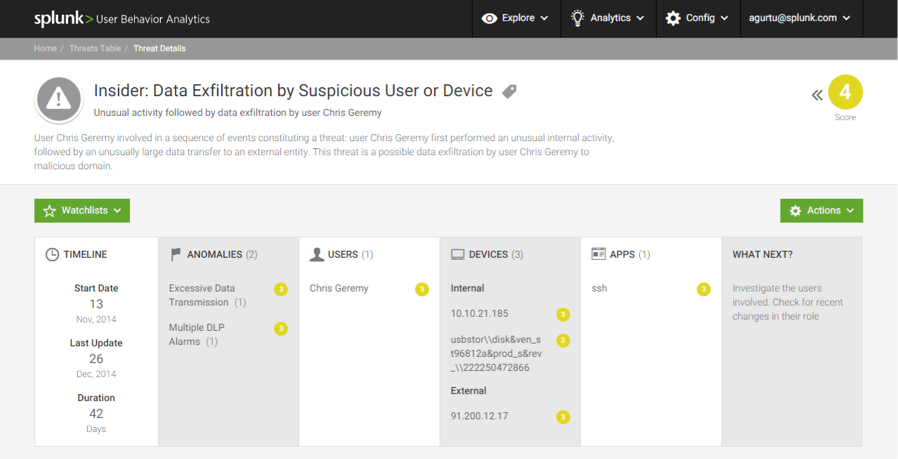
Detailed Visibility
Splunk UBA anomalies provide deep context and visibility across users, devices, applications, and protocols. Statistics computed across these entities help organizations gain better understanding of entities behavior thereby, providing visibility and insight into its activity. In addition, you now have insight into “normal” behavior to better understand your operating environment.
Rapid Investigation of Advanced Threats using Splunk ES 4.1
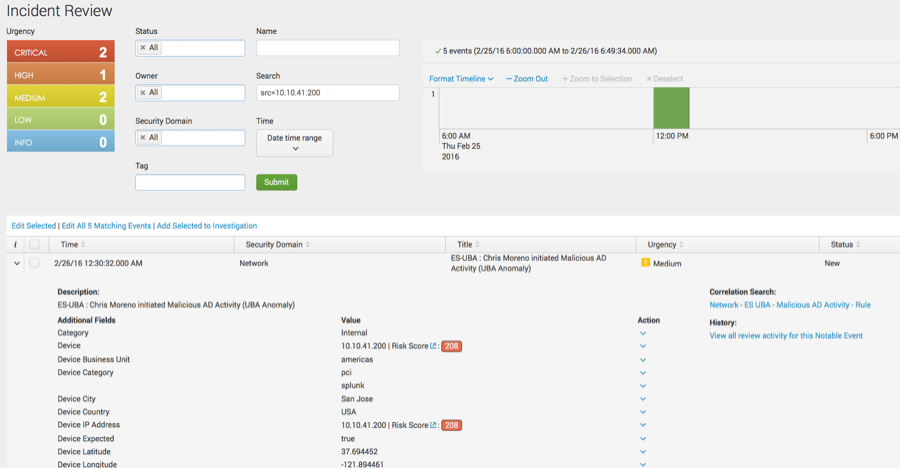
Prioritize and speed investigations
From within the incident review view, Analysts can now use risk scores to determine the impact of an incident quickly and to generate actionable alerts to respond on matters that require immediate attention.
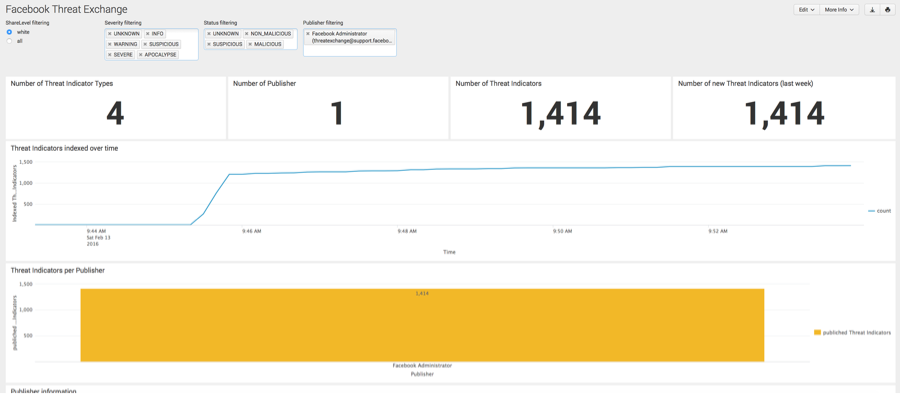
Expands Threat Intelligence Framework with Facebook ThreatExchange
The Splunk ES Threat Intelligence capability is expanded with the addition of the Splunk Add-on for Facebook ThreatExchange. Threat indicators such as domain names, IPs and hashes are derived from Facebook’s massive social platform. Analysts can now use the new ThreatExchange dashboard along with the existing Threat Artifacts and Threat Activity dashboards to assess the threat activity and use the threat indicators with ad hoc searches and investigations.
If you are an Analyst or a CSIRT team member concerned with the speed and efficiency of anomaly detection and Incident Review or if you are a SOC manager who needs detailed information on threat investigations these new capabilities are for your use.
Both Splunk UBA 2.2 and Splunk ES 4.1 are now generally available.
Girish Bhat
Director, Security Product Marketing
Splunk
----------------------------------------------------
Thanks!
Girish Bhat
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.