Overcome Cybersecurity Challenges to Improve Digital Resilience
Security Michael WeinsteinThis blog was co-authored by Michael Weinstein and Casey Wopat.
The idea that digital resilience — the ability to prevent, detect, respond to and recover from disruptive events — is critical to digital business would surprise no one. As the Splunk report Digital Resilience Pays Off illustrates, organizations that are farther along on their digital resilience journey enjoy $48 million lower annual downtime costs and 2 times higher digital-transformation project success rate than their less digitally resilient peers.

Organizations' expanded footprints and the macro environment are, in part, to blame. Cloud adoption and remote work have exponentially increased the attack surface. The pace of onboarding new cloud-based services and resources often surpasses the security team’s capacity to secure them. For example, per the IBM Cost of a Data Breach Report, 2022, 43% of organizations have not started or are in early stages of securing their existing cloud environments. And, according to the Splunk State of Security 2022 report, 65% of companies attribute the measurable increase in cyberattacks to more remote work. At the same time, the cost of a breach is 24.4% higher in organizations with the highest percent of remote employees vs. those with the lowest (IBM Cost of a Data Breach Report, 2022).
62% of the Splunk State of Security 2023 survey respondents stated that their business-critical applications suffered unplanned downtime due to a cybersecurity incident on at least a monthly basis.
Geopolitical tensions have magnified the risk of attacks by sophisticated, nation-state-affiliated actors to the extent that the President of the United States issued a statement warning US businesses about potential malicious cyber activity stemming from the war in Ukraine by Russian actors.
On the receiving end, cybersecurity teams have difficulty keeping up with the increasing volume and sophistication of threats, impacting their organizations’ digital resilience. In fact, 62% of the Splunk State of Security 2023 survey respondents stated that their business-critical applications suffered unplanned downtime due to a cybersecurity incident on at least a monthly basis.
What is hindering cybersecurity teams’ ability to fend off attacks? As is often the case, it is the trifecta of people, process and technology.

Process-wise, cybersecurity workflows are often manual and slow. In order to detect threats and respond to incidents, security analysts need to stitch together data from disparate sources and locations as well as manually orchestrate incident response across disconnected security and IT tools. Such inefficient, error-prone processes hinder security teams’ ability to accurately detect and rapidly respond to threats, giving attackers a leg up. Accordingly, organizations face an average dwell time of 2.24 months, or about nine long weeks, per Splunk State of Security 2023.
As far as technology is concerned, companies use a multitude of security tools from different vendors, which complicates cybersecurity operations. Per the Gartner 2020 CISO Effectiveness Survey, 78% of cybersecurity leaders have 16 or more tools in their portfolio. Accordingly, Splunk State of Security 2023 highlights that 64% of SOC teams struggle to pivot from one security tool to the next, with little integration between the tools to make it easier.
Another technology-related challenge pertains to data. As organizations continue their cloud journeys, data sources become more decentralized and data formats more diverse. Data that may be critically important for security analysis is frequently stored within the IaaS, SaaS or PaaS infrastructure in which it is created or consumed. Moving such data into a security analytics tool for further scrutiny may be cumbersome and costly. Consequently, security teams often find it challenging to include, for example, cloud data stores into the threat detection, investigation and response processes, creating blind spots in security coverage and hindering the organization’s ability to mitigate threats. Further, various systems and sources may produce data in different formats, so security teams often need to dedicate time and effort to normalizing data before it can be analyzed, which takes up resources and slows down threat detection, investigation and response.
Embracing automation, unifying security operations and tackling security as a data problem helps organizations overcome the challenges that talent shortage, inefficient processes and disconnected security tools and data sources pose to cybersecurity effectiveness, hence to digital resilience.
With this doom and gloom, the question arises about how cybersecurity teams can effectively contribute to their organizations’ digital resilience despite talent shortage, inefficient processes and disconnected technology and data stack? The approach that Splunk and its customers have been successfully using involves automating and unifying security operations and tackling security as a data problem.
Automating Security Operations to Address Talent Shortage and Process Inefficiencies
Automation enables scalable, repeatable and compliant processes to help analysts accelerate incident investigation and response across tools, teams and environments, eliminate human error and avoid burnout. With automation, security, IT and DevOps teams can collaborate on issues in near real-time, enabling rapid incident resolution.
Automation also acts as a force multiplier, allowing understaffed security teams to do more. For example, a combination of in-depth phishing analysis and attack-chain following capabilities of Splunk Attack Analyzer with automation delivered by Splunk SOAR enables analysts to completely automate the analysis of malware and credential-phishing threats and free up time for other projects.
Unifying Security Operations to Solve the Challenges of Disconnected Multi-Vendor Tools
Bringing all security operations into a single console helps expedite threat detection, investigation and response by saving analysts time and effort on context switching between disparate security products. Accordingly, Splunk Mission Control provides a single common work surface that allows analysts to manage the security incident lifecycle more efficiently.
Tackling Security as a Data Problem to Detect Threats Across Decentralized and Diverse Data Sources
Addressing security as a data problem is critical to countering advanced attacks by APTs and other sophisticated threat actors. Stealthy by design, advanced attacks stay below security tools’ alarm thresholds, generating mostly “weak” signals. So, advanced attack detection hinges on the security team’s ability to identify and correlate such “weak” signals. Since “weak” signals can come from anywhere in the organization, all enterprise data can contain clues of advanced attacks, hence needs to be monitored and analyzed for security purposes.

With the ability to rapidly consume and analyze data from all enterprise sources and prioritize threats according to the risk they pose to the organization, security teams can maximize their attack-surface coverage and reliably detect advanced attacks.
To help security teams save time and effort on normalizing disparately formatted data, Splunk has partnered with AWS and other industry leaders to create the Open Cybersecurity Schema Framework (OCSF) open source project that provides a common vendor-agnostic taxonomy to simplify and accelerate data ingestion and analysis. For example, Amazon Security Lake stores data in the OCSF format and acts as a single data feed for multiple AWS and partner sources. Amazon Security Lake data can be brought directly into Splunk in the OCSF format or will soon be easily searchable in its original locations using Splunk federated search.
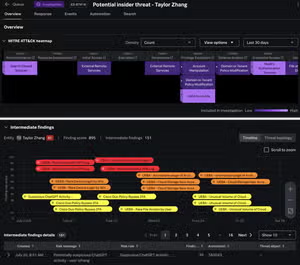
To enable accurate detection, contextualization and prioritization of threats, Splunk Enterprise Security delivers continually updated detections and integrates threat intelligence and ML models. Enterprise Security’s Risk-Based Alerting (RBA) functionality transforms a multitude of alerts into a few high-fidelity notables, prioritized by organizational risk to prevent analysts from drowning in alert noise and enable them to investigate and resolve issues faster. RBA also helps pinpoint threats that would be difficult to detect with traditional correlation searches. It places events that would traditionally yield isolated low fidelity, low criticality alerts in the context of related risky behaviors. By looking at the interplay of alerts and behaviors, security analysts can detect low-and-slow attacks that previously may have been missed.
With the ability to rapidly consume and analyze data from all enterprise sources and prioritize threats according to the risk they pose to the organization, security teams can maximize their attack-surface coverage and reliably detect advanced attacks by making sense out of “weak” signals regardless of which data sources they come from. Plus, by having all data in one place, security teams can effectively collaborate with IT and DevOps teams to rapidly identify the root cause of disruptions and performance issues.
Embracing automation, unifying security operations and tackling security as a data problem helps organizations overcome the challenges that talent shortage, inefficient processes and disconnected security tools and data sources pose to cybersecurity effectiveness, hence to digital resilience. Learn more about how government agencies and businesses all over the world are benefiting from this approach.
Related Articles

PCI Compliance Done Right with Splunk

Cloud Federated Credential Abuse & Cobalt Strike: Threat Research February 2021