Security Blogs
Latest Articles
template
category
category
security
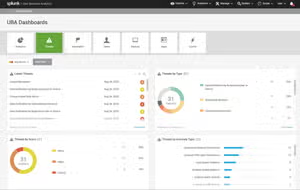
Elevating Security Intelligence with Splunk UBA's Machine Learning Models
Splunk UBA uses machine learning to detect evolving threats beyond rule-based approaches in SOC operations, tackling overwhelming event volumes.

Enhancing SIEM Events with Automated Threat Analysis of URLs
Splunk debuts Add-on & App for Splunk Attack Analyzer v1.1, elevating security ops via automated URL threat analysis in Splunk ES.

Detecting New Domains in Splunk (Finding New Evil)
Ready to find "new" domains that may be naughty? We'll walk you through how to use Splunk & Splunk Enterprise Security to do that: get the full story here!

Under the Hood of SnakeKeylogger: Analyzing its Loader and its Tactics, Techniques, and Procedures
In this blog, the Splunk Threat Research Team provides valuable insights to enable security analysts and blue teamers to defend and be aware of these scam tactics.

Security Insights: JetBrains TeamCity CVE-2024-27198 and CVE-2024-27199
The Splunk Threat Research Team examines exploit operations, analytics, hunting queries, and tips on capturing TeamCity logs.

Add To Chrome? - Part 4: Threat Hunting in 3-Dimensions: M-ATH in the Chrome Web Store
SURGe experiments with a method to find masquerading using M-ATH with Splunk and the DSDL App.

Detect Money Laundering, Healthcare Fraud, and Unemployment Fraud with the New Version of the Splunk App for Fraud Analytics
Detect money laundering, healthcare fraud, and unemployment fraud with Splunk App Fraud Analytics 1.2.4.

Staff Picks for Splunk Security Reading February 2024
The Splunk security team shares a curated list of presentations, whitepapers, and customer case studies they feel are worth a read.

Beyond Logs: Navigating Entity Behavior in Splunk Platform
Master internal threat detection with Splunk's anomaly detection, finding events like unusual geolocations and spikes in activity, while optimizing security.