Latest Articles
displayMode
paginated
category
Security
showImagesOnMobile
false

Security
10 Minute Read
CitrixBleed 2: When Memory Leaks Become Session Hijacks
Discover how to detect, mitigate, and respond to CitrixBleed 2 (CVE-2025-5777), a critical Citrix NetScaler ADC and Gateway vulnerability exploited in the wild.
Security
20 Minute Read
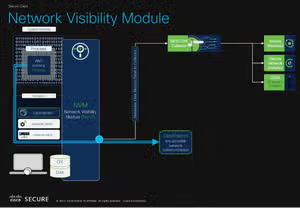
Unlocking Endpoint Network Security Insights with Cisco Network Visibility Module (NVM) and Splunk
Unlock deep endpoint network security insights by integrating Cisco NVM with Splunk.
Security
13 Minute Read
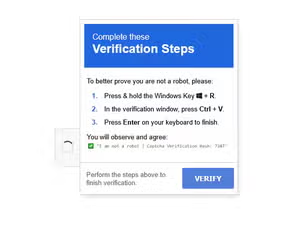
Beyond The Click: Unveiling Fake CAPTCHA Campaigns
Learn how clipboard hijacking delivers malware and explore tools like ClickGrab & PasteEater for robust defense strategies.

Security
4 Minute Read
Splunk @ SAPPHIRE 2025 Recap: How SAP Customers Use Splunk for World-Class Observability and Security
Splunker Keith Hontz shares a look at the Splunk highlights from SAP SAPPHIRE 2025.

Security
2 Minute Read
Splunk Security Content for Threat Detection & Response: June Recap
Learn about the latest security content from Splunk.

Security
6 Minute Read
How To Use CloudTrail Data for Security Operations & Threat Hunting
This blog post reviews AWS cloudtrail as a security logging source and how to hunt in it

Security
16 Minute Read
When Installers Turn Evil: The Pascal Script Behind Inno Setup Malware Campaign
Uncover the Inno Setup malware campaign leveraging Pascal scripting to deliver RedLine Stealer.

Security
4 Minute Read
Threat Hunting with TLS/SSL Certificates
TLS and SSL certificates are a great way to hunt advanced adversaries. Collect them with Splunk Stream, Bro, or Suricata and hunt in your own data!

Security
4 Minute Read
Hunting with SA-Investigator & Splunk Enterprise Security (SIEM)
Discover how Splunk Enterprise Security and the SA-Investigator add-on empower analysts to streamline threat hunting and incident response. Learn how to pivot across assets, identities, and processes for deep-dive investigations and actionable insights. Happy hunting!