Latest Articles
displayMode
paginated
category
Security
showImagesOnMobile
false

Security
3 Minute Read
Introducing Splunk Attack Range v3.1
The Splunk Threat Research Team is happy to release v3.1 of Splunk Attack Range.

Security
3 Minute Read
Vulnerability Prioritization Is a Treat for Defenders
There have been numerous high-profile cybersecurity incidents where vulnerability management had an impact on severe breaches – here are some notable examples.

Security
14 Minute Read
PowerShell Web Access: Your Network's Backdoor in Plain Sight
The Splunk Threat Research Teams dives deep into PowerShell Web Access (PSWA) exploring its functionality within the context of cyber threats.

Security
2 Minute Read
Splunk is Nurturing Tomorrow’s Cybersecurity Leaders Today
The Splunk Academic Alliance program combines education with practical skills development to prepare the next generation of data and cybersecurity professionals.

Security
6 Minute Read
Macro-ATT&CK 2024: A Five-Year Perspective
Splunk’s Ryan Fetterman and Tamara Chacon dive into attacker techniques, trends, and blue team tips for analyzing and visualizing data from the past year.

Security
3 Minute Read
Cybersecurity Awareness Is Not Just for Spooky Season
As October marks Cybersecurity Awareness Month, Splunker Mick Baccio reflects on the progress made over the past two decades.

Security
11 Minute Read
My CUPS Runneth Over (with CVEs)
This blog dissects the technical intricacies of the CUPS vulnerability, explores its potential impact on affected systems, and provides detection opportunities and mitigation strategies.

Security
11 Minute Read
A Case Study in Vulnerability Prioritization: Lessons Learned from Large-Scale Incidents
Splunker Audra Streetman provides an overview of the lessons learned from previous large-scale security incidents to help inform vulnerability prioritization.
Security
5 Minute Read
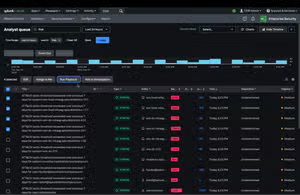
Splunk SOAR Evolved: A Unified TDIR Approach to Automation
Splunk SOAR 6.3.0 and 6.3.1 constitute a significant evolution in how security practitioners can implement, use, and leverage security automation in the SOC more efficiently.