Guided Automation Using Real Incident Data for Easier Playbook Building in Splunk SOAR
Security Patriz RegaladoSecurity automation should allow a security team to execute a collection of actions across threat detection, investigation and response in seconds, versus minutes or hours if performed manually. A phishing investigation typically requires the execution of multiple actions across several security tools and takes 40 minutes to complete. Using security automation from Splunk SOAR, that 40-minute process can now be completed within 60 seconds or less. In this way, an automation tool like Splunk SOAR can drastically reduce mean time to detect (MTTD) and mean time to respond (MTTR).
Furthermore, a SOAR user interface should be intuitive and user-friendly, and automated playbooks should be painless to create and modify. Features like playbook editors should allow for both source code editing and visual editing. To accelerate time-to-value and streamline new hire onboarding and training, SOAR tools should have embedded assistive capabilities to help analysts rapidly get started — and get comfortable — with playbook development. This allows all security team members — regardless of preference or coding expertise — to construct comprehensive and sophisticated playbooks.
Splunk SOAR provides all of the above, and has long offered a feature-rich, powerful visual playbook editor that enables customers to build highly sophisticated automations, with custom code if necessary. While we acknowledge the importance for this customizability, we’re also focused on making automation faster, easier and more accurate. It’s important to remember that automation isn’t a one-size fits all solution — low code options are only effective when the automation author has a clear understanding of both the data and the process flow.
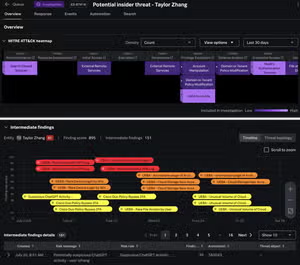
With Guided Automation, a new feature in the recently released Splunk SOAR version 6.3.1, playbook building is easier than ever. Guided automation unlocks a whole new visual experience overlaying real incident data atop the logical sequencing in a playbook. This superimposition not only drastically reduces the time to build automation but also improves accuracy as you can see output results in each individual playbook block based on real incident data.
Now, security analysts and automation engineers can:
- Build automation playbooks more easily with intuitive at-a-glance data visualizations that show data in the context of specific security investigations
- Build faster with suggested actions to quickly add the right action blocks, filters, and prompts with a single click
- Build accurately by visualizing results rooted in real data from individual blocks
These enhancements ensure that automation playbooks are built and deployed rapidly to protect organizations from ever-evolving threats.
Of course, you have to see it to believe it. Watch this demo.
Experience guided automation with the latest version of Splunk SOAR. Check out our Tech Talk, watch the webinar, or dive into release notes.
Related Articles

Parsing Domains with URL Toolbox (Just Like House Slytherin)
Strengthen SOC Defenses with Native UEBA in Splunk Enterprise Security
