
Digital Resilience Pays Off
Download this e-book to learn about the role of Digital Resilience across enterprises.
 I started wearing prescription glasses my freshman year of high school—after all that time eating carrots and not staring too hard at my Gateway PC (remember those?!), my genetics finally caught up to me. For me, contact lenses are reserved for special occasions (i.e. when I actually have five minutes to spare by putting them in my eyeballs), so 99 percent of the time, I see the world through good ol’ polycarbonate lenses. So when anti-reflective coating for my lenses became available, it was a no-brainer to make the switch. Even though I could *see* just fine without it, my vision was refreshed—my world became a little brighter and a little clearer by making this subtle change.
I started wearing prescription glasses my freshman year of high school—after all that time eating carrots and not staring too hard at my Gateway PC (remember those?!), my genetics finally caught up to me. For me, contact lenses are reserved for special occasions (i.e. when I actually have five minutes to spare by putting them in my eyeballs), so 99 percent of the time, I see the world through good ol’ polycarbonate lenses. So when anti-reflective coating for my lenses became available, it was a no-brainer to make the switch. Even though I could *see* just fine without it, my vision was refreshed—my world became a little brighter and a little clearer by making this subtle change.
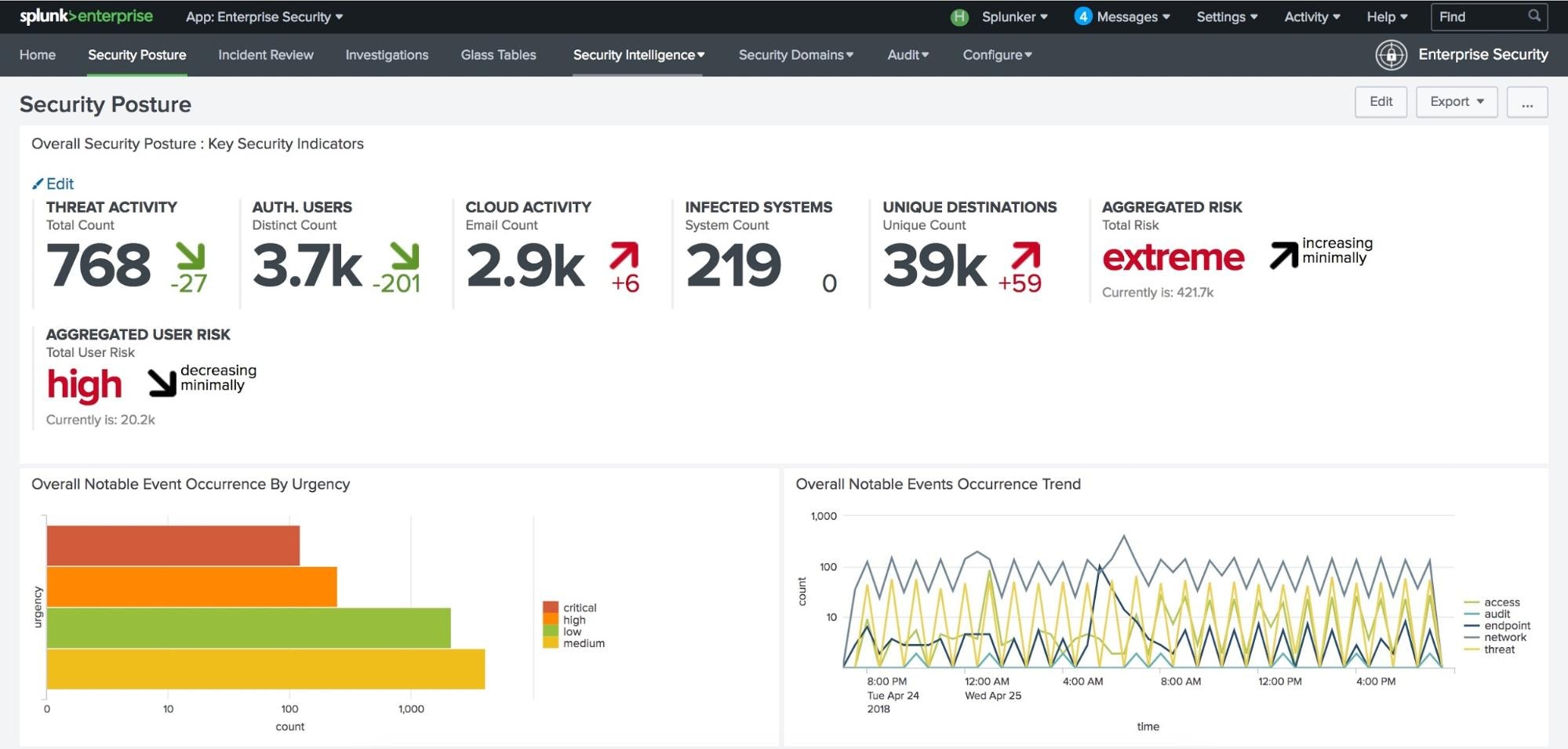
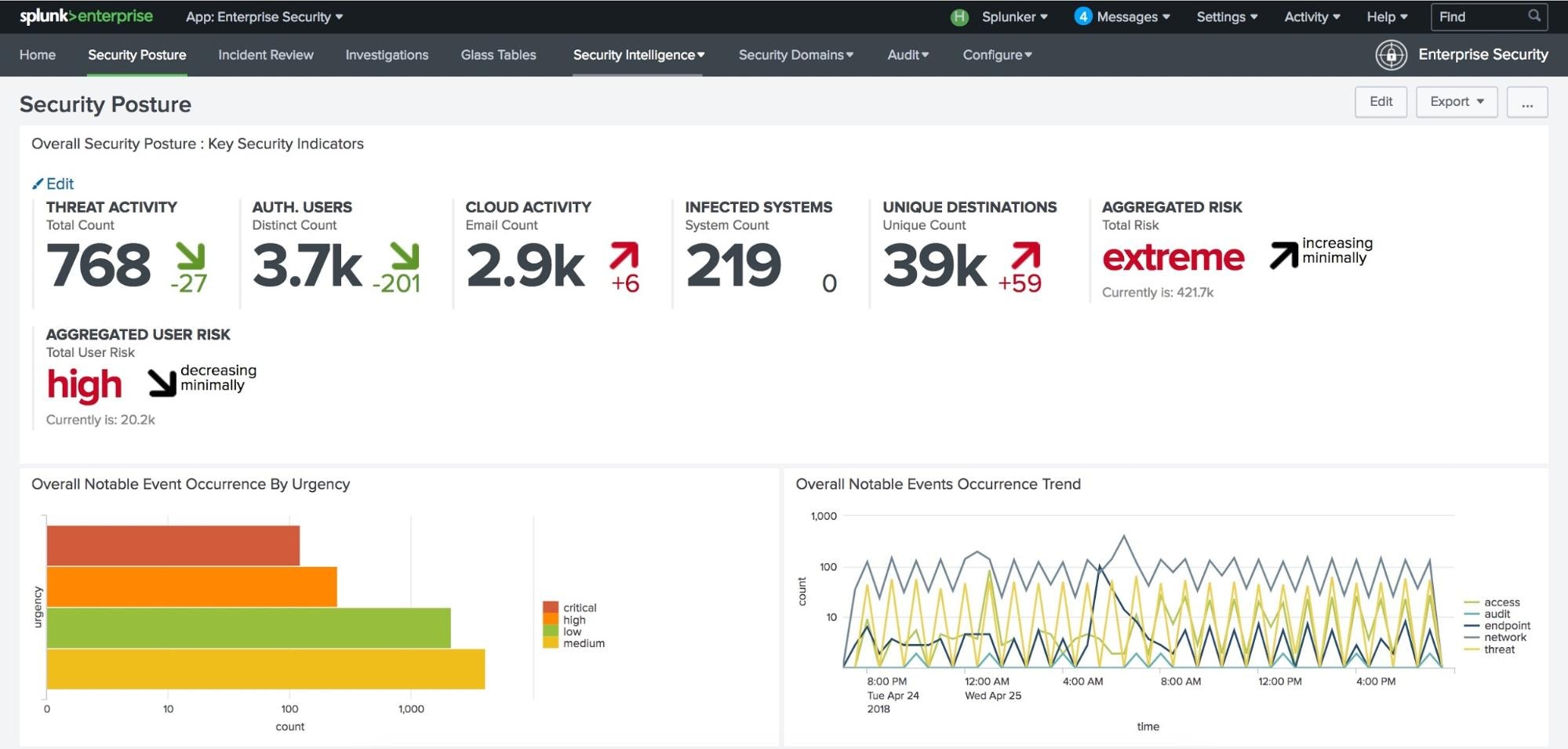
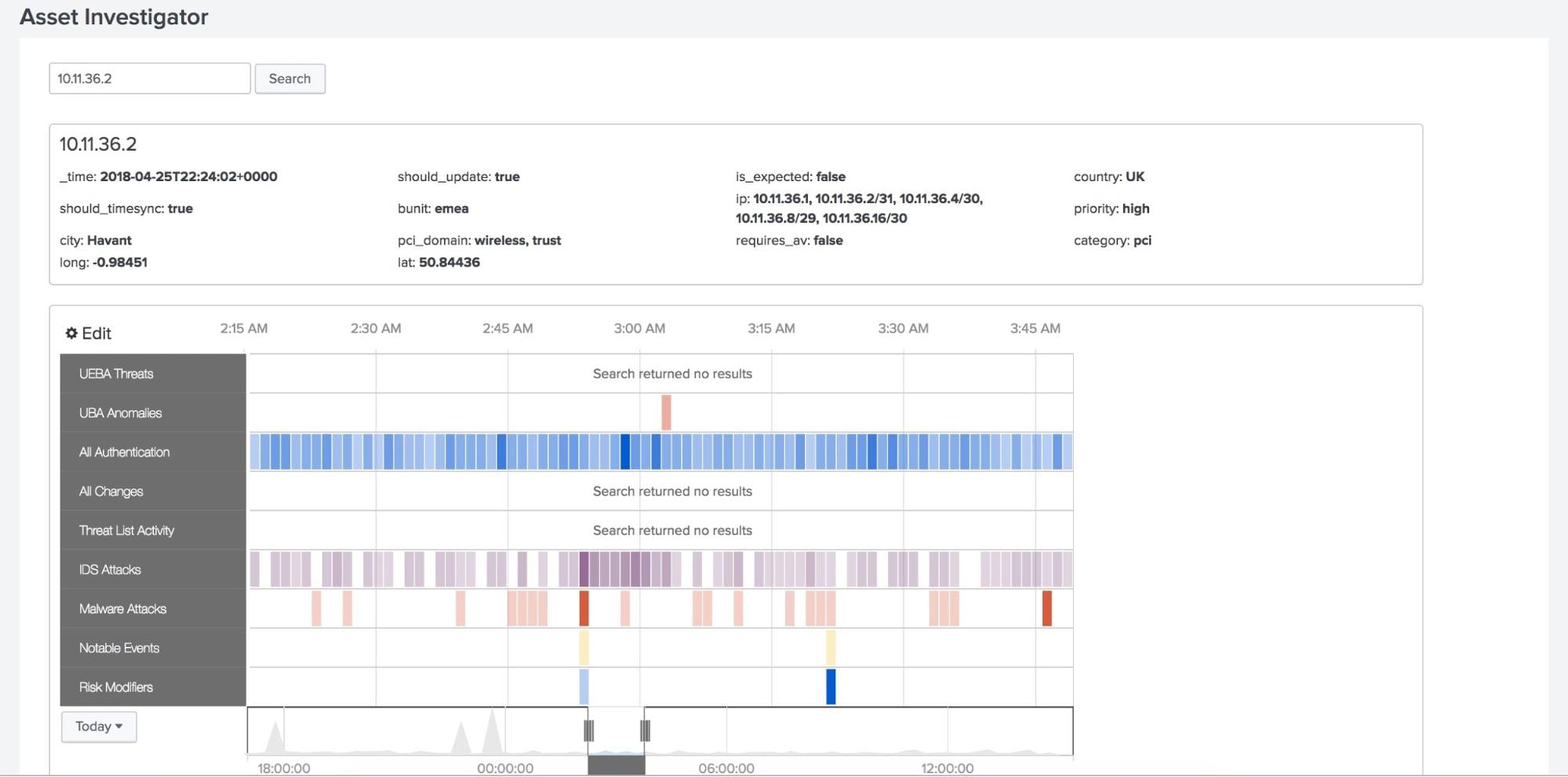
In a similar fashion, today, we released Splunk Enterprise Security 5.1 which features a subtle but significant change: a visual refresh compatible only with Splunk Enterprise 7.1. Coming off the heels of the advancements made in some of our flagship products and services, security teams will be able to see their environment in a brighter and clearer interface, while still in the context of the analytics-driven SIEM workflow within Splunk Enterprise Security.
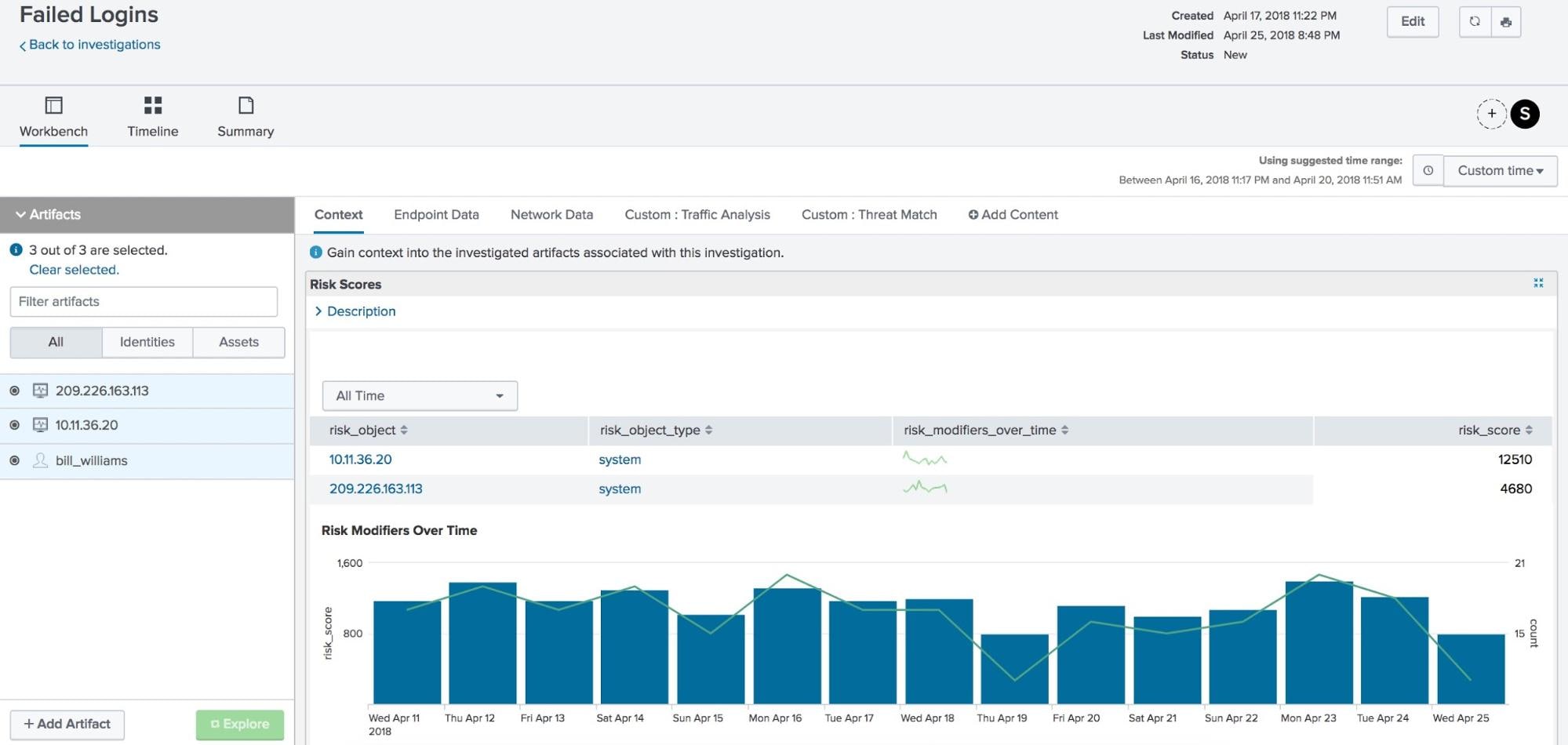
Never underestimate the importance of a good UI! Even the most skilled SIEM professionals find it difficult to build actionable dashboards, alerts, and reports with a legacy product (amongst other things). Take our friends at TransAlta. Their previous solution struggled with these problems, along with the inability to perform advanced correlations or fast security investigations. With Splunk Enterprise Security, TransAlta was able to see fast time-to-value with investigation times reduced from days to minutes.
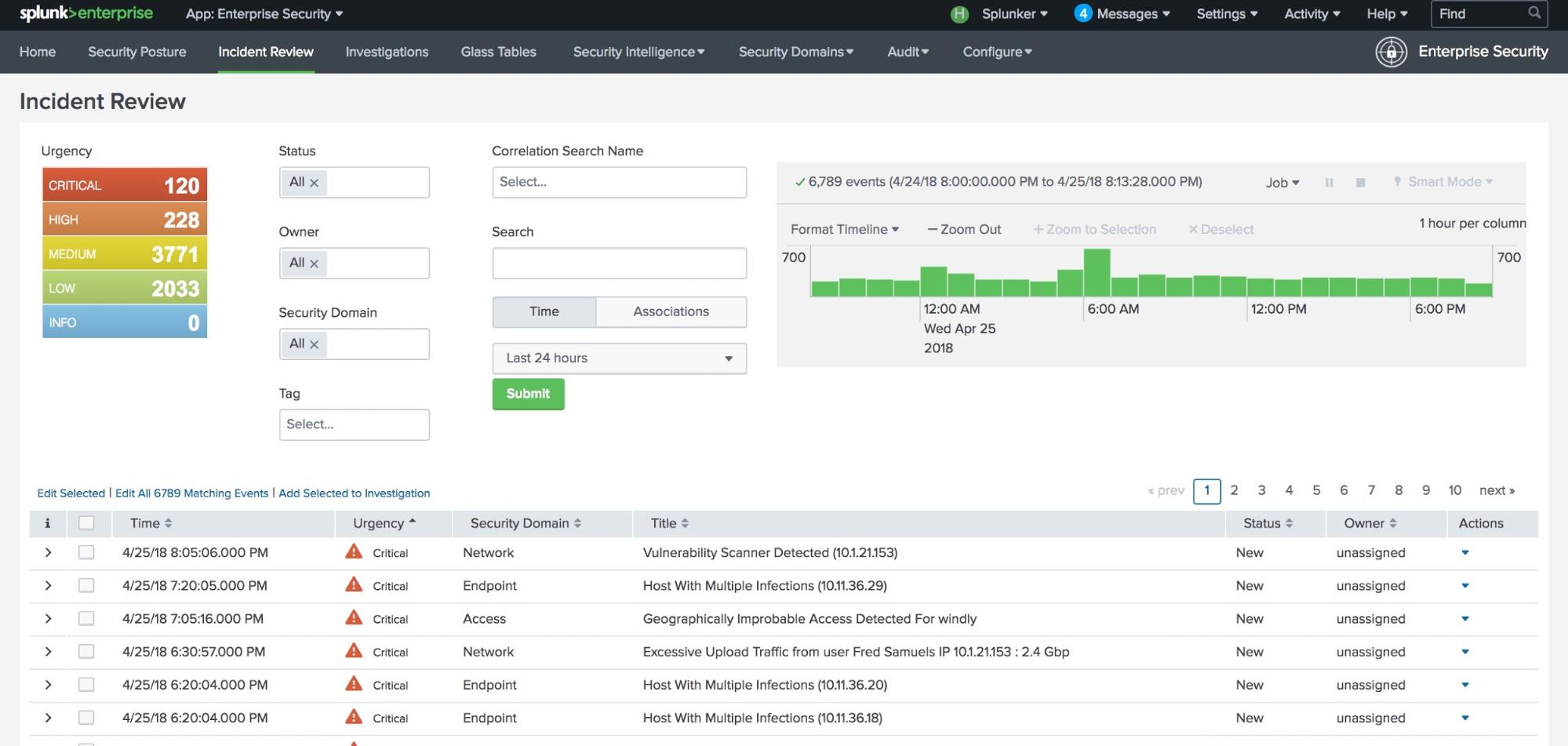
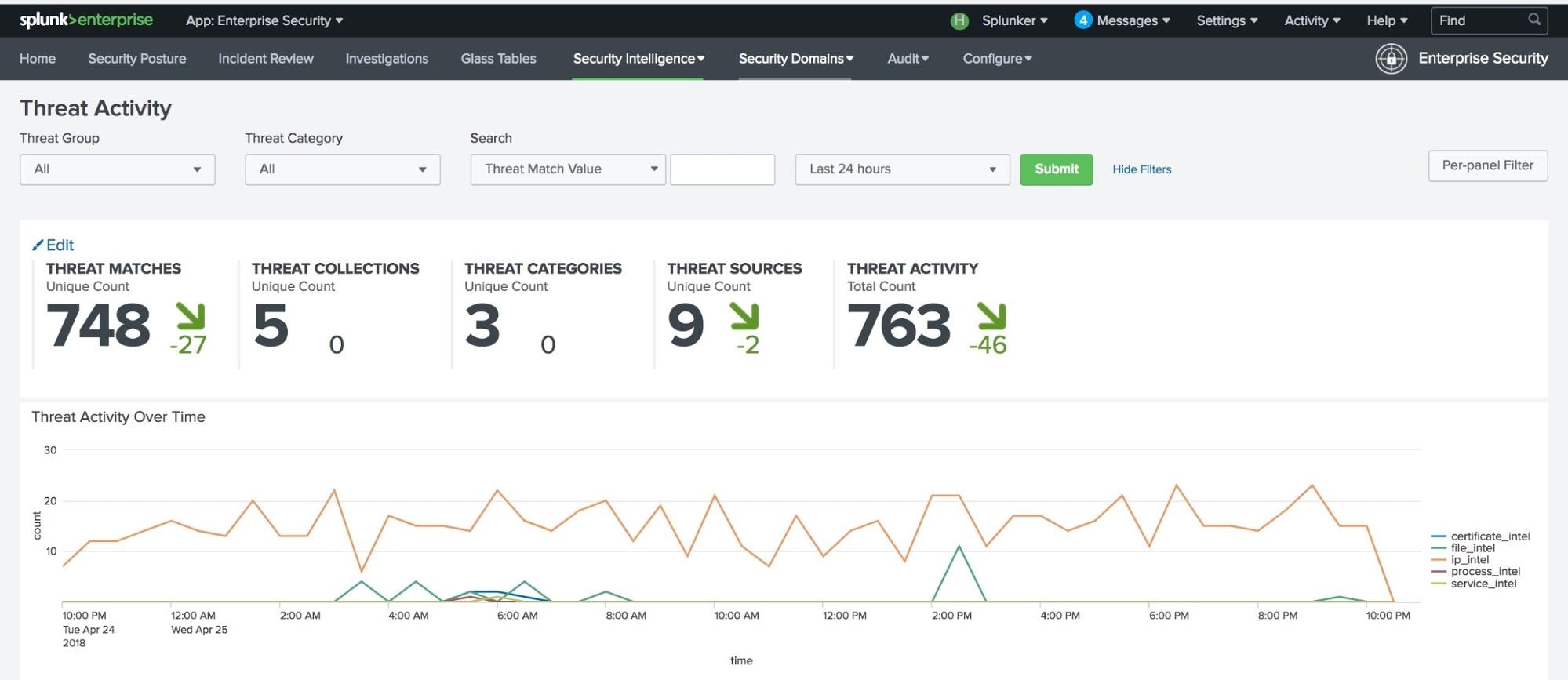
The end-to-end visibility that Splunk Enterprise Security provides becomes visually impactful in version 5.1. Visualizations, alert actions, and notable events have clearer lines, smoother colors, and crisper fonts. This makes prioritizing and managing threats and uncovering anomalies a more polished experience.
Eighty-nine percent of organizations say their cybersecurity function does not fully meet their needs (Source: EY GISS 2017-18). Customers like Heartland Automotive have met their needs by implementing Splunk, gaining visibility across their ecosystem as well as the ability to:
• Centralize and aggregate all security-relevant data sources
• Correlate and alert across all data sources
• Provide fast searching and reporting
• Streamline incident investigations
• Accelerate incident response
• Add context and threat intelligence to security events
If you’re an existing Splunk ES customer: You will need to download Splunk Enterprise 7.1 before upgrading to Splunk ES 5.1 (available now on Splunkbase), since critical compatibility advancements have been made under-the-hood.
If you’re not familiar with Splunk ES, I encourage you to try out our free online sandbox.
Contact us if you want to see your security environment more clearly.
Happy Splunking!
Alexa
----------------------------------------------------
Thanks!
Alexa Araneta
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.