Splunk is actively working towards achieving FedRAMP High Authorization in the next 12 months.
Mission-ready with defense and intelligence technology solutions
Defense and intelligence agencies need technologies that provide a competitive advantage to support successful missions — be it protecting the homeland, keeping the peace in a war-torn country or delivering humanitarian relief. All four branches of the U.S. military and many agencies in the intelligence community already rely on Splunk to make confident decisions and take decisive action at mission speeds.
As an IL5-approved software-as-a-service (SaaS) offering, DoD mission partners can rapidly field, accredit and operationalize Splunk’s platform for security information and event management (SIEM), AIOps and compliance risk management framework (RMF) use cases. Lengthy ATO times also are dramatically reduced because stringent DoD controls are already implemented per IL5 requirements. As part of the DOD’s Enterprise Software Initiative (ESI), U.S. Government agencies can now easily order and use Splunk Cloud Platform for higher sensitivity Controlled Unclassified Information (CUI).
- Continuously monitor your infrastructure and protect against advanced external and insider threats.
- Gain real-time situational awareness in theater of operations.
- Improve mission efficiencies through performance monitoring and reporting.
- Ensure compliance with various mandates for accountability, security and procurement.
- Predict and resolve issues before they impact the mission with AI/ML technologies.
- Protect your data’s confidentiality, integrity and availability in compliance with government security requirements such as FedRAMP Moderate and IL5. Learn about compliance at Splunk.
Get Started
Guidance & Research
- The SOAR Buyers Guide
- Compliance Essentials for Splunk
- What Is Risk Management?
- Splunk Executive and Emerging Technologies Predictions
- The Essential Guide to JADC2
- Splunk for Risk Management Framework
- Splunk for Cybersecurity Maturity Model Certification
- Splunk Receives Provisional Department of Defense Impact Level 5 Authorization
- How Visibility Accelerates Successful IT Modernization in the Public Sector
- Leveraging Splunk for U.S. DoD IL5
- How Splunk Supports the DoDs Zero Trust Strategy
Enhance your SOC with award-winning security solutions
Splunk Wins Third Ever NAVWAR Enterprise Artificial Intelligence Prize Challenge for Exceptional SOAR Capabilities

Get real-time insights
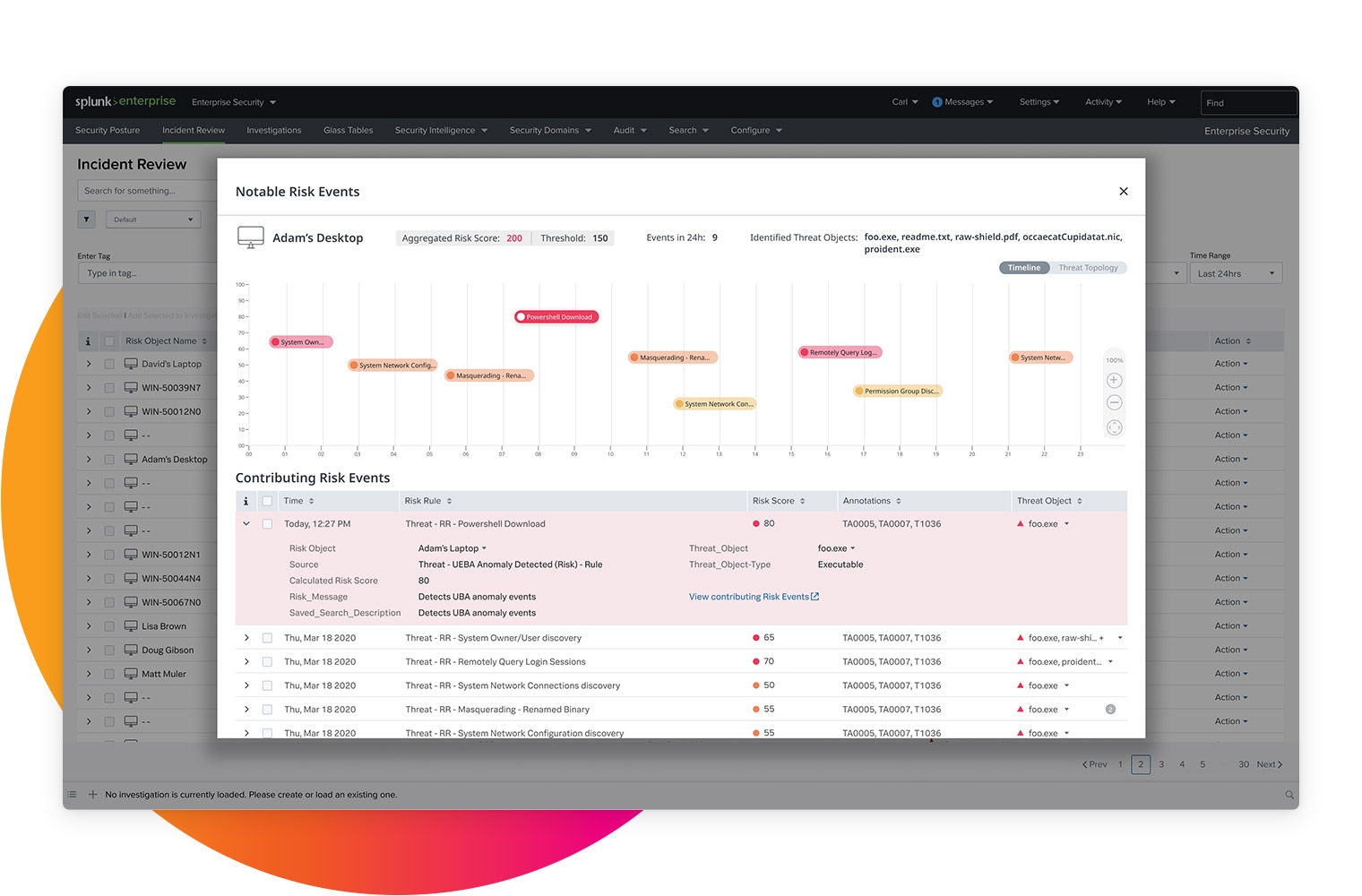
When problems arise, defense leaders must act quickly and decisively. Splunk equips organizations with real-time, full visibility into their environments so they can get the insights they need as soon as they need them — no matter how complex the technological environment. Easily monitor, detect and mitigate anomalous activities with a unified view of your data. Learn more about Splunk’s FedRAMP-authorized and IL5-compliant products.
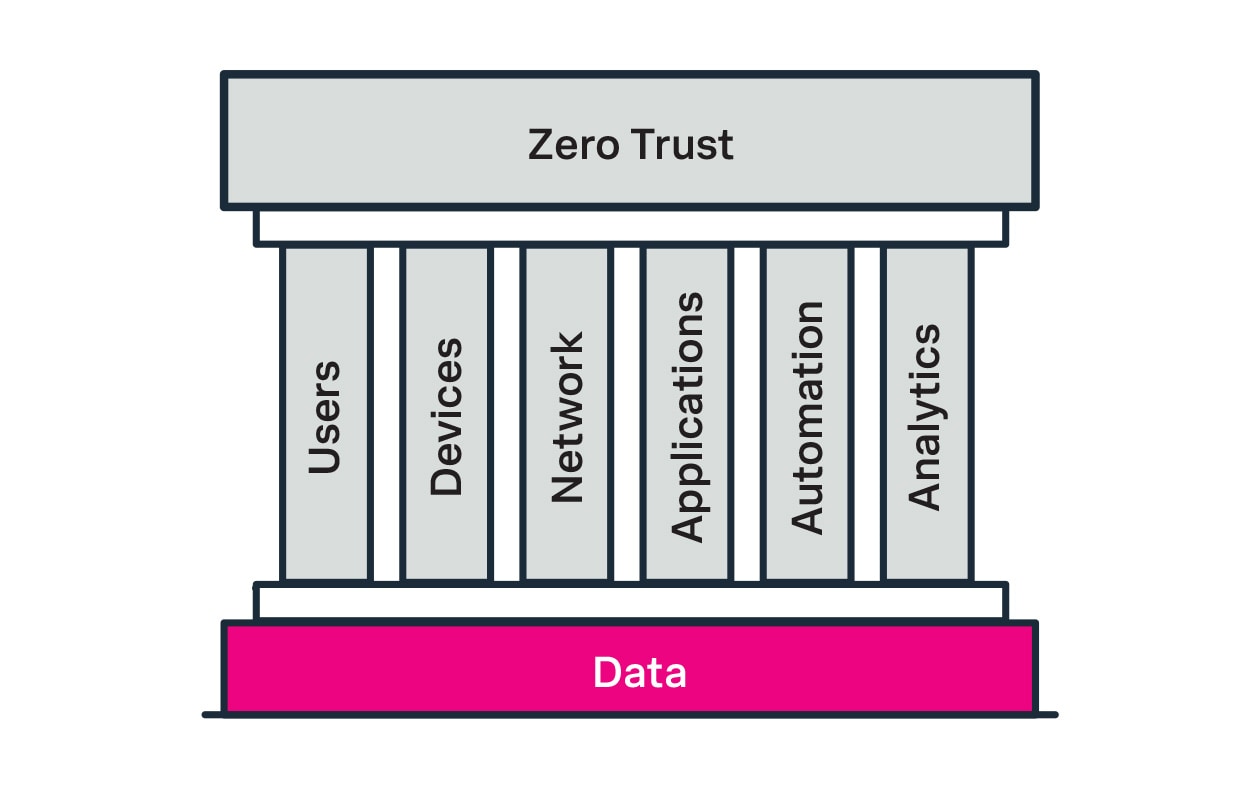
Establish zero trust
To enhance security and abide by Executive Order 14028, agencies need the right tools for creating a zero trust architecture. Splunk, a proven public sector partner, can help establish that security foundation. The Splunk platform allows agencies to analyze any data source at any scale, and helps teams keep systems secure and healthy with continuous monitoring — even in hybrid environments. Securely consume threat intelligence and increase confidence that only trusted users can access your systems, so you can focus on the mission at hand.
Optimize cybersecurity
Traditional perimeter-based defense approaches are ill-equipped to handle today's security threats from nation-states, sophisticated cyber criminals and insiders. Siloed products and a skills and resource shortage are compounding the challenge. With the Splunk platform, agencies can automate their security operations at scale to pinpoint malicious activity quickly and respond to incidents fast through an intuitive, integrated interface.
Modernize legacy systems
Splunk provides public sector professionals with FedRAMP-authorized services* so it’s faster and easier to move to the cloud and execute IT modernization initiatives. Splunk Cloud Platform has been granted provisional authorization for use at the Information Impact Level 5 (IL5) as specified by the Department of Defense/DISA Cloud Computing Security Requirements Guide. This authority allows defense organizations to use Splunk Cloud Platform capabilities and accommodates higher-sensitivity intelligence.
*at the Moderate Impact Level





